Cyber deception is the most effective way to identify threat actors in any organization’s network. CounterCraft delivers actionable threat intelligence across industries.
-
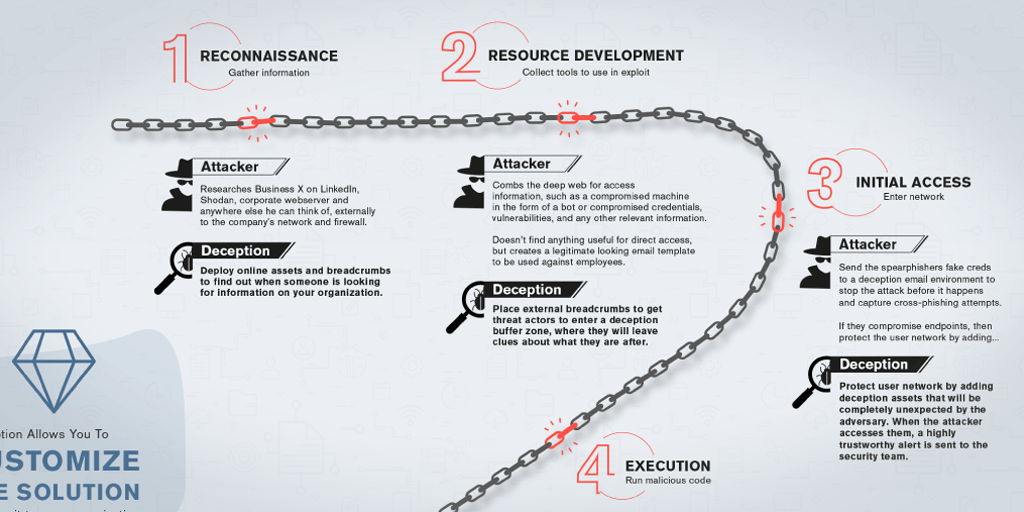
{INFOGRAPHIC} The Anatomy of a Cyber Attack
This infographic breaks down the stages of a typical cybersecurity incident and shows you how to stop it. Read more
-
Categories: Deception Technology
What We’re Reading
Cybersecurity news in April. Click through to find out what our team of experts was reading and talking about this month. Read more
-
The Anatomy of a Cyber Attack
Every cyber attack consists of various stages, from pre breach to the moment of impact. We believe every stage is an opportunity to trip up and trap cyber criminals. Keep reading to get a breakdown of the stages of a typical cybersecurity incident.100 character intro: An infographic that shows how a typical cybersecurity incident unfolds. Read more
-
Why Threat Intel is Broken
The purpose of threat intelligence is to gather information that helps you understand an attacker so that you can proactively take action against them. The current generic threat intel won’t help get you to that goal. Deception will. 100 character intro: Generic threat intel just isn’t enough to keep systems secure. Read more
-
Categories: Deception Technology
How to Activate ActiveBehavior | Threat Deception in A Minute
Threat Deception in a Minute highlights just how simple it is to get powerful deception technology set up in your network. Whether you’re a current customer or wondering what it’s like to utilize deception, you’ll find these videos quick, interesting and helpful. 100 character intro: See just how simple it is to get powerful deception… Read more
-
Deception for Industrial Control Systems
Industrial Control Systems (ICS) have many unique characteristics that make defensive countermeasures against cyber attacks a challenging job. Cyber deception can be a great way to protect these assets without imposing any burden on the normal operation of services. Read more