Cyber deception is the most effective way to identify threat actors in any organization’s network. CounterCraft delivers actionable threat intelligence across industries.
-
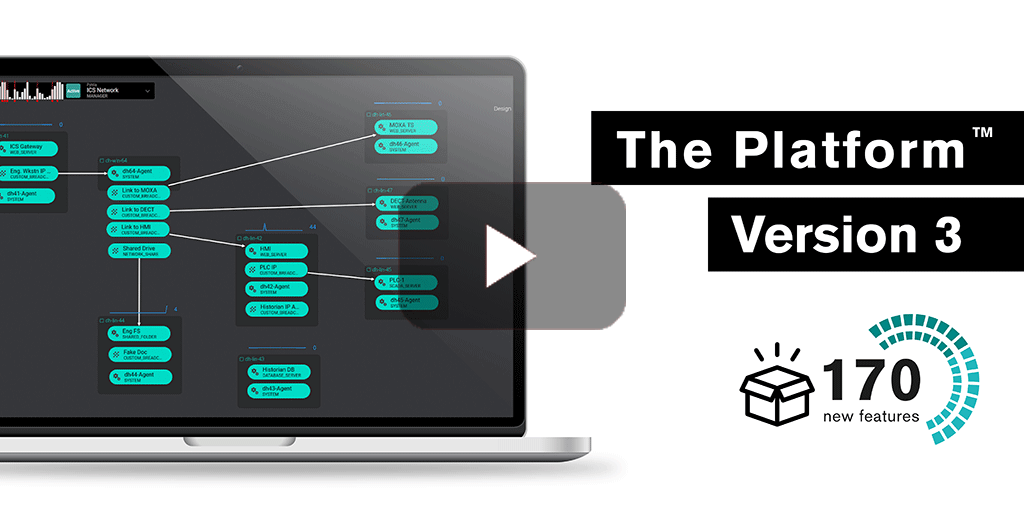
{VIDEO} Detect and Mitigate Threats Faster with New Features
CounterCraft The Platform™ V3 revolutionizes the way security teams deploy and analyze deception campaigns, thanks to more than 170 new features focused on our customers’ needs and designed to actively defend their organization’s cybersecurity posture. Read more
-
The Platform v3: Now with Attack Trees to Implement Sophisticated Active Defense
CounterCraft The PlatformTM v3 revolutionizes the way security teams deploy and analyze deception campaigns, thanks to more than 170 new features focused on our customers’ needs and designed to actively defend their organization’s cybersecurity posture. Read more
-
Categories: Deception Technology
What We’re Reading
Cybersecurity news in January. Click through to find out what our team of experts was reading and talking about this month. Read more
-
Cybersecurity in Banking: Global Bank Uses CounterCraft to Detect Lateral Movement in a SWIFT Network
CounterCraft helps mitigate threats to cybersecurity in the banking industry. To learn more about how deception helped our client to detect and respond to attacks on their SWIFT network, download the full case study here Read more
-
Categories: Deception Technology
What We’re Reading
Cybersecurity news in December. Click through to find out what our team of experts was reading and talking about this month. Read more
-
Deception Technology in the Cyber Domain | Nicole Carignan at AUSA CyberWorld 2022
Nicole Carignan, Head of Customer Success at CounterCraft, spoke at AUSA CyberWorld 2022 about deception technology in the cyber domain. In this presentation, Carignan gives an inside look at the unique technology behind CounterCraft’s deception platform and explains how your organization can gather adversary-generated threat intelligence Read more