Cyber deception is the most effective way to identify threat actors in any organization’s network. CounterCraft delivers actionable threat intelligence across industries.
-
Categories: Threat Intelligence
A Step-by-step BPFDoor Compromise
During the last few days there have been many articles describing BPFDoor, a UNIX backdoor allegedly used by Chinese threat actors. BPFDoor is a smart backdoor that does not need to open additional ports when the attacker wants to connect to the compromised host. It is able to hijack current open ports, sniff the traffic,… Read more
-
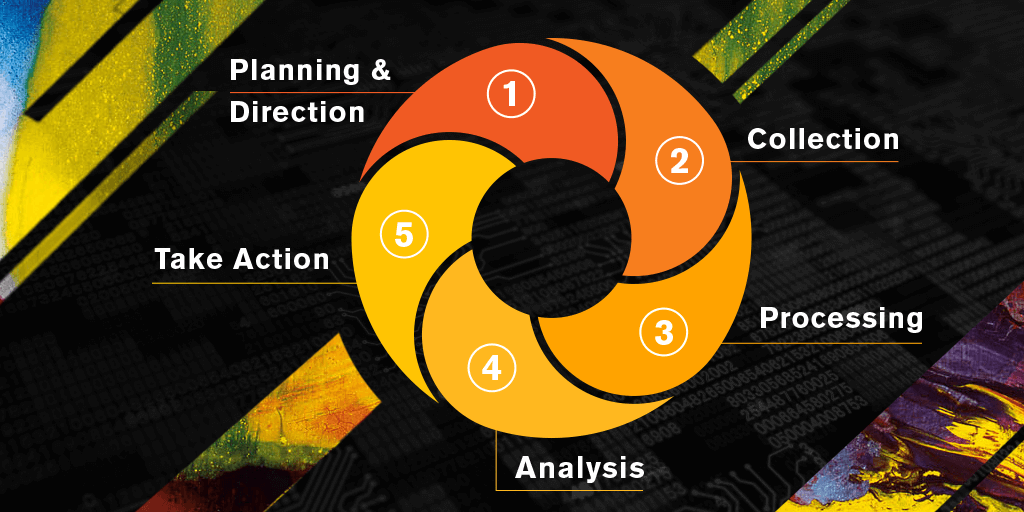
The Threat Intelligence Lifecycle 2.0
Generic threat intel wastes a lot of time. As technology evolves, so does the threat actor. Threats and techniques change on a daily basis, making the job of the cyber defender incredibly difficult. Our approach to threat intel is the use of deception technology to collect real-time threat intel specific to your environment. This is… Read more
-
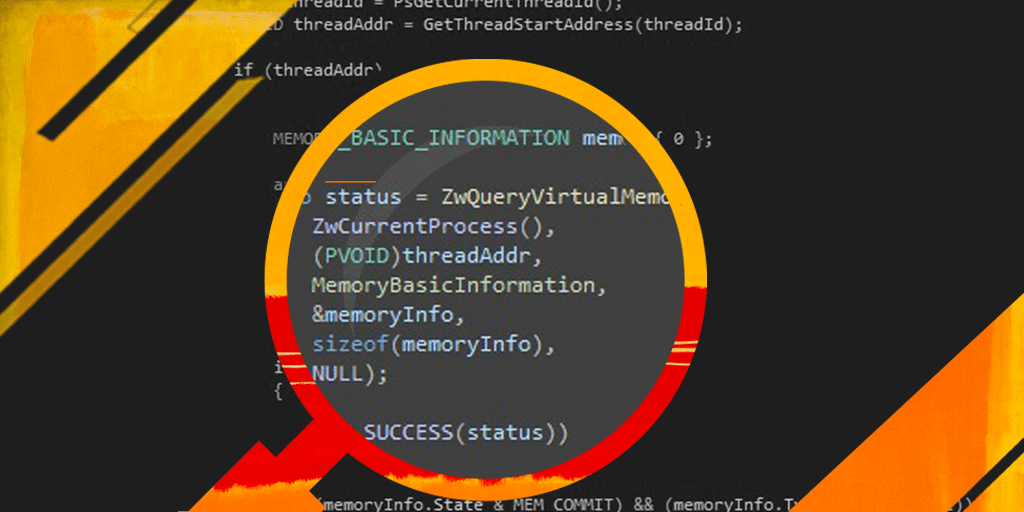
Detecting malicious artifacts using an ETW consumer in kernel mode
Post-exploitation tooling is becoming increasingly sophisticated and often evades detection by EDRs, meaning sometimes we will not be able to detect when an attacker is able to load his code into memory. Here’s a way to detect artifacts that are already loaded in memory from kernel and in real time Read more
-
Categories: Threat Intelligence
IOCs from the Attacks on Ukrainian Government Infrastructure
See the IoCs from a recent attack on Ukrainian Government Infrastructure, a very interesting incident carried out by exploiting CVE 2021 4034 and detected by our deception environments Read more
-
Categories: Threat Intelligence
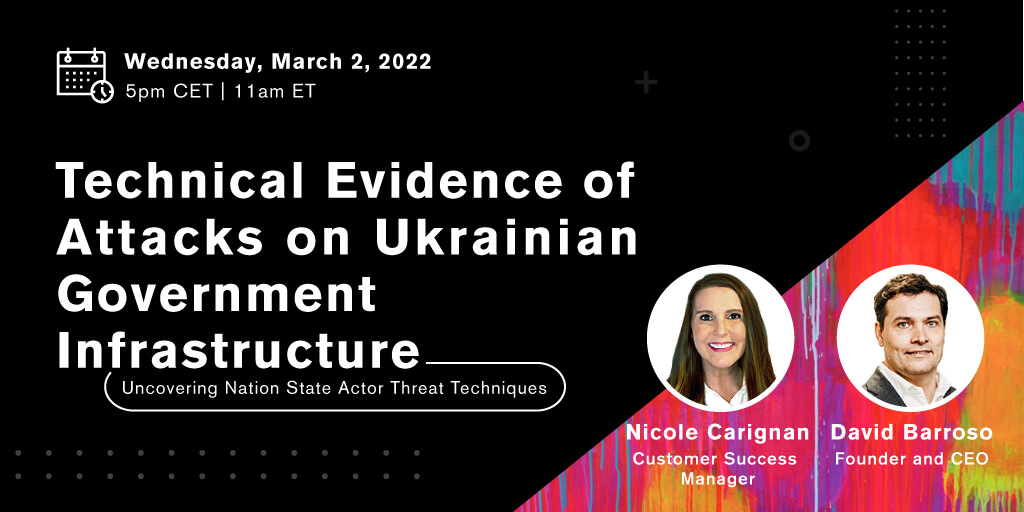
{Webinar} Technical Evidence of Attacks on Ukrainian Government Infrastructure
Join a webinar on March 2, 2022 about the technical evidence our deception directors have picked up of attacks on Ukrainian government infrastructure, featuring our Customer Success Manager Nicole Carignan and CEO David Barroso Read more
-
Cobalt Strike Explained—What it is and How to Detect it | Founder Chat
The founders of CounterCraft talk about Cobalt Strike and how to detect it. Watch the video Read more