Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
Stay One Step Ahead with Adversary-Generated Threat Detection Read more

-
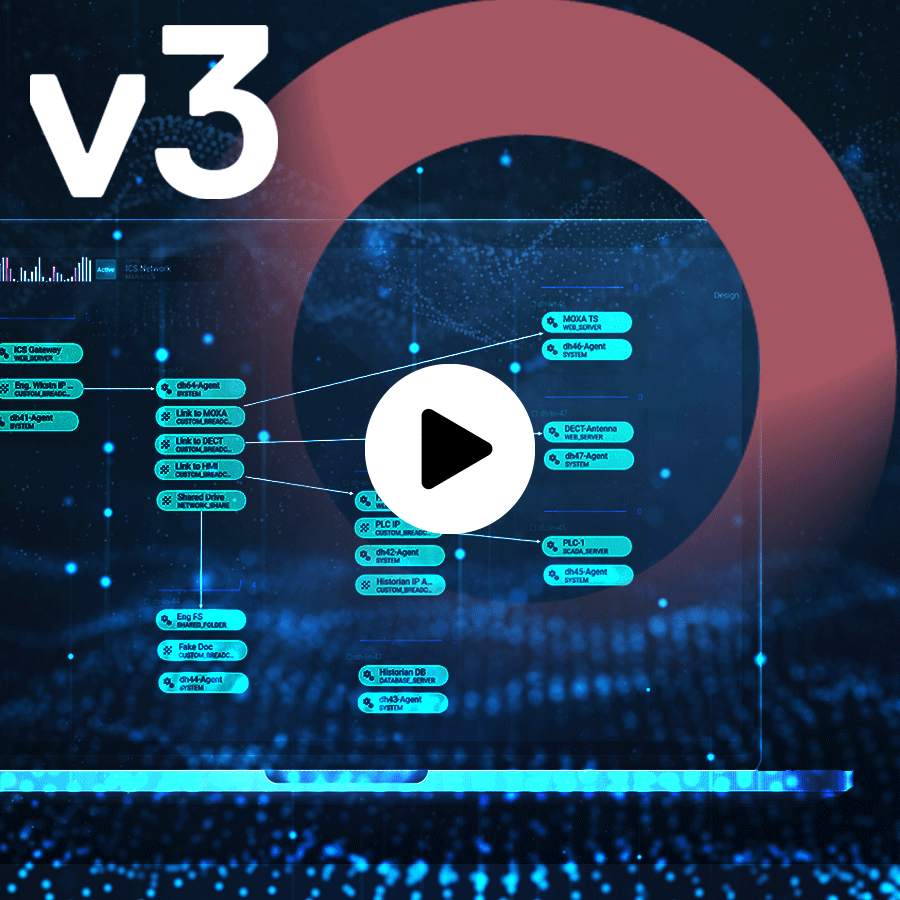
ICS security is challenging. See how Red Electrica used deception technology to prevent attacks on their OT systems. Read more
-
Define your organizational zero trust strategy armed with deception technology to prevent breaches and gain powerful adversary threat intelligence. Read more

-
Define your organizational zero trust strategy armed with deception technology to prevent breaches and gain powerful adversary threat intelligence. Read more
-
ICS security is challenging. See how Red Electrica used deception technology to prevent attacks on their OT systems. Read more

-
ICS security is challenging. See how Red Electrica used deception technology to prevent attacks on their OT systems. Read more