Looking to strengthen your OT security?
Look no further.
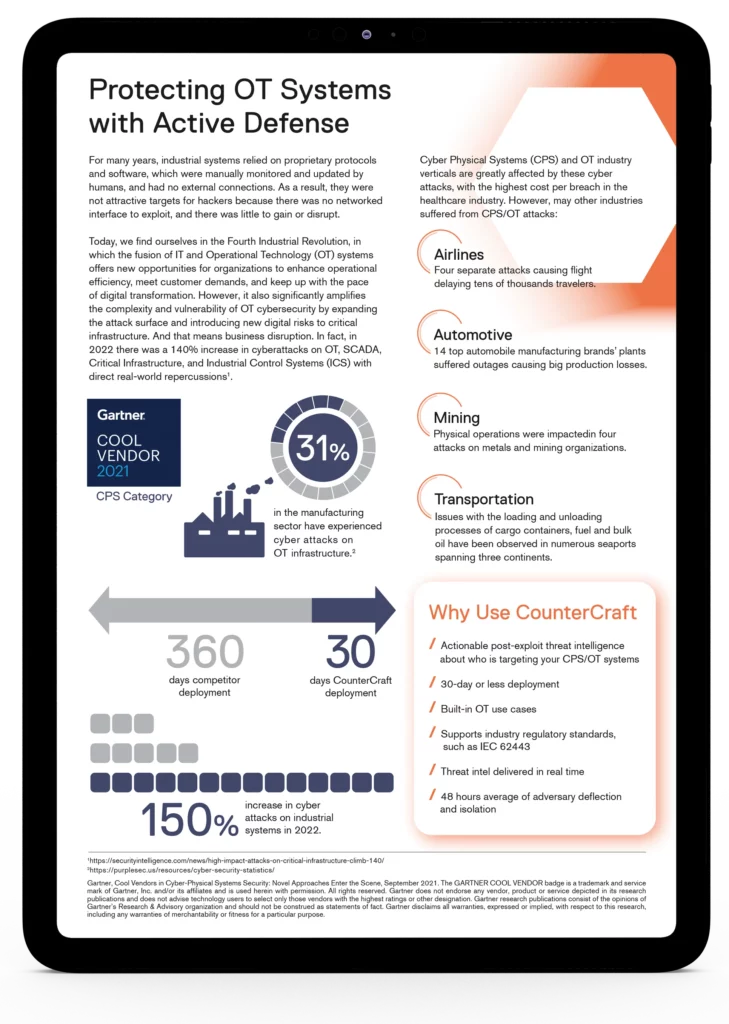
Operational Technology (OT), SCADA, Critical Infrastructure (CI), and Industrial Control Systems (ICS) networks are difficult to defend. Download this datasheet to read about how cyber deception is uniquely positioned to face the challenges inherent in these environments.
Get it now.
Fill out this form to receive the datasheet Protecting OT Systems with Active Defense. The information inside will help you and your organization detect, deter, document, and defend against cyberattacks.
“The use of outdated and physically isolated devices, and the convergence between the IT and the OT world, make these environments vulnerable to insider threats and external breach attempts.”
What’s inside?
Concerned about OT security vulnerabilities?
Find out how deception technology provides proactive protection of critical assets without imposing any burden on the normal operation of services.
Due to increasing attacks on critical infrastructure and physical systems, countermeasures against cyber attacks are crucial. OT environments are a critical operational component and can be difficult to defend. Integrated deception solutions make it easy to create critical infrastructure deception campaigns with zero disruption to business continuity.
This datasheet explains all the common challenges and offers accessible & automated security solutions. Download it now to find out how to protect your OT, SCADA, CI, and ICS networks and get real-time threat intelligence.
Download now.
Detect, deter and defend against cyberattacks.
