Incorporating Deception into Your XDR Framework: A Game-Changing Approach
Download this whitepaper to learn exactly how cyber deception works to complete and supercharge XDR, complementing and exponentially increasing its effectiveness.
Get it now.
Fill out this form to download the whitepaper and learn how your organization can detect, deter, document, and defend against cyberattacks.
“Deception deflects adversaries while collecting real-time intelligence, multiplying the power of XDR.”
Download the whitepaper to get :
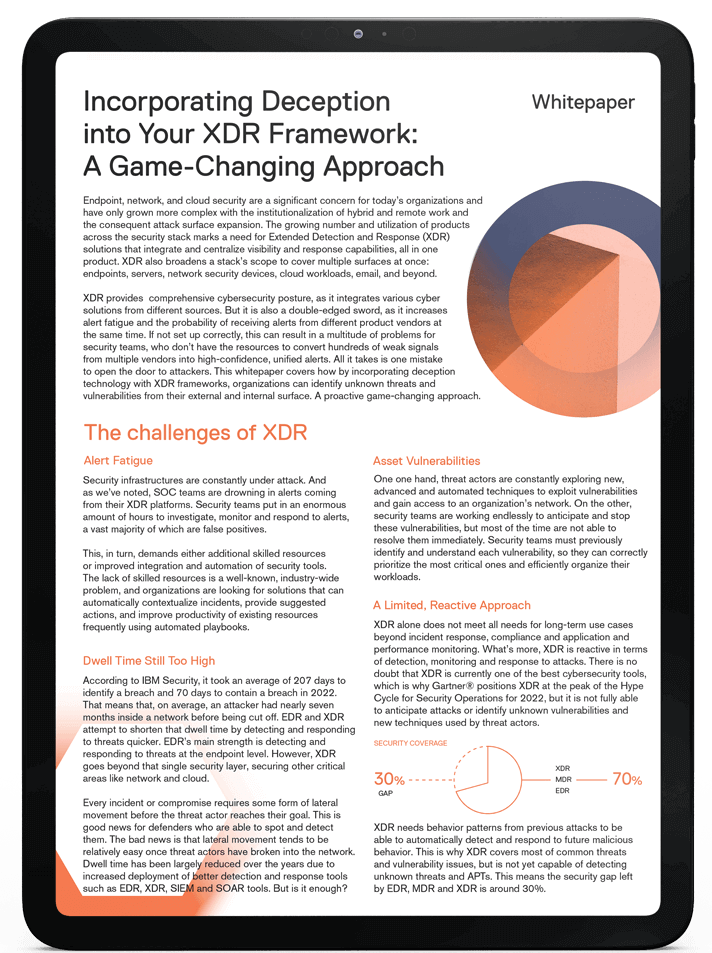
If you don’t have a cyber deception solution as part of your XDR strategy, 3 out of 10 attackers could waltz right in.
XDR needs behavior patterns from previous attacks to be able to automatically detect and respond to future malicious behavior. This is why XDR covers most of common threats and vulnerability issues, but is not yet capable of detecting unknown threats and APTs. This means the security gap left by EDR, MDR and XDR is around 30%.
This whitepaper covers how by incorporating deception technology with XDR frameworks, organizations can identify unknown threats and vulnerabilities from their external and internal surface. A proactive game-changing approach.
Download now.
Detect, deter and defend against cyberattacks.