
How exposed is your retail environment to today's cyber threats?
Most security teams can tell you what they monitor, but far fewer can answer what they would actually see during a live intrusion. That’s where the real gaps are – and where attackers quietly succeed.
We built a 5-minute, self scored assessment to change that.
This assessment is designed specifically for retailers like yourself and focuses on one thing only: what you would actually see today if valid credentials were abused. Helping you identify the five visibility gaps that matter most.
Start the assessment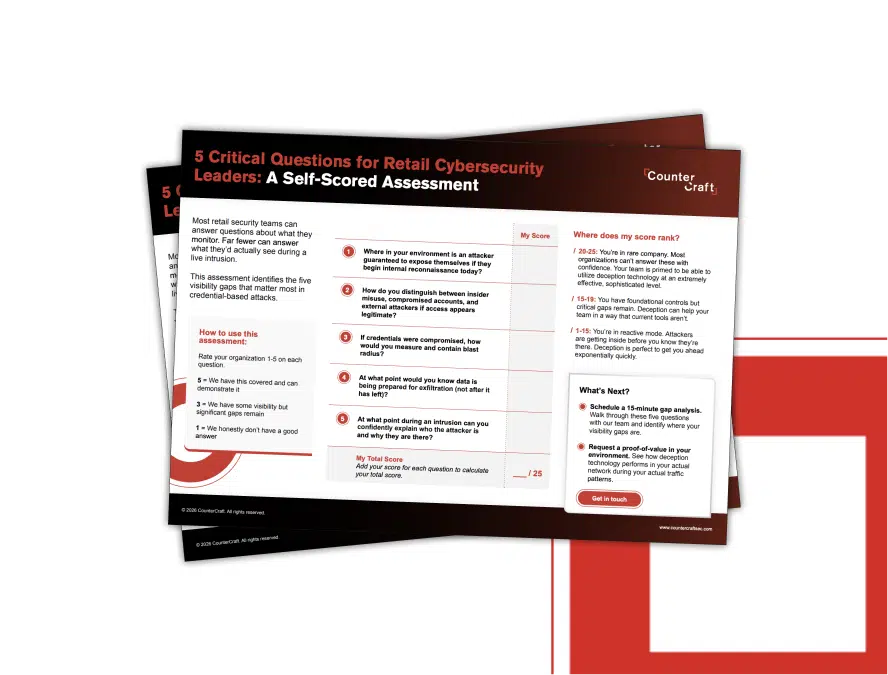
Get it Now
Fill out this form to receive your retail assessment sheet. Figure out where you rank with our scoring guide and get concrete insights into your visibility gaps that will help you and your organization detect, deter, document, and defend against cyber attacks.
Why Use This Assessment?
This is a concise, actionable guide to help benchmark your organization’s ability to detect and respond to modern threats. Particularly those that exploit credentials, move laterally, or exfiltrate sensitive data without triggering alerts – the most common in retail industries.

Measure visibility, not assumptions:
Go beyond basic monitoring checks to understand where your defenses truly stand

Identify real risk gaps:
Learn which areas of your environment leave attackers free to move undetected

Score and compare:
See where your answers place you on a simple scoring scale. From reactive to advanced readiness.

What You’ll Get
-
/1
A short, self-scored, question set tailored to retail environments. Focussing on visibility into attacks before, during, and after they unfold.
-
/2
A quick way to spot blind spots that could be exploited in credential abuse and lateral movement
-
/3
Insight into how well your current security posture would reveal attacker behavior in real-time
What’s Next?
Choose from the below options and reach out to our team of specialists to help start your deception journey with confidence.
Schedule a 15-minute gap analysis
Schedule a 15-minute gap analysis
Walk through these five questions with our team and identify where your visibility gaps are.
Request a proof-of-value in your environment
See how deception technology performs in your actual networks during your actual traffic patterns.
Get in touch today