Honeypots are decoy systems that attract attackers and signal malicious activity. Most, however, are low-interaction and simplistic. Sophisticated adversaries detect and bypass them quickly. Organizations that want real, actionable threat intelligence need advanced deception platforms built to solve the problems honeypots never could.
A honeypot is a cybersecurity tool designed to attract attackers by mimicking a real system. When an adversary interacts with one, defenders gain a signal that something is wrong. In theory, this sounds powerful. In practice, honeypots have always been more limited than their reputation suggests.
The concept dates back to the late 1980s, and for decades, honeypots were largely confined to academic research. They were difficult to maintain, easy for skilled attackers to detect, and rarely capable of generating the kind of deep, actionable intelligence that security teams actually need. Security teams already struggling to patch their real systems had little bandwidth to maintain a convincing fake one alongside them. As one analogy puts it: if your house is on fire, you are not going to build a fake house next door to see if the arsonist strikes there first.
Understanding why honeypots fall short is essential to understanding what modern deception technology actually is, and why organizations that lead in threat intelligence have moved well beyond them.
What is a Honeypot in Cybersecurity?
A honeypot is a decoy system designed to imitate legitimate infrastructure inside an IT environment.
The name reflects the strategy. Just as honey attracts bees, a honeypot attracts attackers by presenting something that appears valuable: exposed services, interesting data, or credentials that look worth stealing.
Security teams deploy honeypots inside a network, isolated from production systems. Because no legitimate user should ever interact with a honeypot, any connection signals malicious activity. False positives are rare.
When attackers interact with a honeypot, they may reveal:
- Which vulnerabilities they attempt to exploit
- The commands they execute after gaining access
- What tools or malware they deploy
- Which systems they attempt to reach next
The gap between what honeypots promise and what they deliver in practice, however, is significant.
How do Honeypots Work?
Honeypots work by presenting attackers with a system that appears vulnerable and worth exploring.
Defenders configure the honeypot to simulate systems that attackers commonly target: outdated services, unpatched systems, or usable-looking credentials. Attackers discover them during reconnaissance, using scanning tools to probe networks for open services or misconfigurations. When a honeypot responds like a real system, it attracts attention.
Once inside, attackers treat the honeypot like a real target, and every action is theoretically recorded: commands, payloads, exploitation attempts.
“They stimulate services rather than running real software, which means the data they capture is shallow and their behavior is easier for experienced adversaries to identify as artificial.”
Most honeypots, though, are low-interaction systems. They simulate services rather than running real software, which means the data they capture is shallow and their behavior is easier for experienced adversaries to identify as artificial. High-interaction honeypots, which run real software and allow attackers to move freely, generate richer intelligence, but they are expensive and complex to build and sustain. In practice, most organizations that try to run them struggle to keep them convincing over time.
What are the Benefits of Using Honeypots?
Early Detection
When an attacker breaches a system, they don’t usually seek to cause damage immediately. Instead, they explore the environment. They scan networks, test access points, and search for systems they can exploit. Honeypots expose these behaviors early.
Placed correctly inside a network, honeypots act as tripwires. When attackers probe the environment during reconnaissance or attempt to move between systems, the decoy becomes an attractive target. That interaction alerts defenders before the attacker reaches critical infrastructure.
High-Confidence Alerts
Security teams often struggle with alert fatigue. Many detection tools generate large numbers of warnings that turn out to be harmless activity.
Honeypots work differently. Because legitimate users should never access them, any interaction with a decoy is a clear, actionable signal that needs to be followed up. This helps teams focus their resources where it matters most.
Improved Incident Response
The decoy slows attackers down, distracting them from valuable assets. While adversaries are investigating the honeypot, it buys time for defenders to analyze their activity and strengthen their defenses.
What are the Limitations of Honeypots?
The traditional honeypot struggles against experienced adversaries and modern attack techniques.
Detection by Attackers
Today’s sophisticated attackers actively test systems to determine whether they are genuine targets. Low-interaction honeypots are particularly vulnerable. These systems rely on emulation rather than on real software, making them easier to identify.
Attackers may detect inconsistencies in system behavior, network responses, or service configuration. Once identified as a trap, the honeypot loses its value. The attacker simply avoids it.
Maintenance Overhead
A honeypot must remain convincing to attract attackers. This requires regular updates and careful configuration. Systems that look outdated, incomplete, or poorly maintained raise suspicion. Without continuous upkeep from security teams, the decoy quickly becomes ineffective.
Static Nature
Traditional honeypots are static systems. Once deployed, they cannot change or adapt to attacker behavior. Skilled adversaries often recognize these traps (because their TTPs have improved since the trap was set) and move around them.
Limited Scope
Honeypots only detect attackers who interact directly with them. If an adversary never touches the decoy, the honeypot won’t deliver a signal. This creates blind spots across the wider environment.
Shallow Intel
Even when honeypots do generate data, basic deployments capture only surface-level information: IP addresses, commands, timestamps. Building a picture of attacker TTPs requires a depth most honeypots cannot deliver.
Lack of Integration
Standalone honeypots often sit outside the core detection-and-response pipeline. If they don’t integrate with SIEM or SOAR tools, it limits how far the data can travel and how quickly it can be acted on.
Risk of Misconfiguration
A poorly configured honeypot can create risk rather than reduce it. Threats include:
- Permissive rules that turn a decoy into an entry point
- Weak isolation that allows attackers to access production assets
- Poor monitoring that gives adversaries a place to hide
Why Honeypots Alone Aren’t Enough
Modern adversaries increasingly rely on automated tools, AI-assisted malware, and ransomware frameworks that operate at high speed. These tools are designed to test environments quickly and determine whether a system is genuine before investing time in exploitation. A basic honeypot can be identified in milliseconds.
Beyond speed, the core problem is structural. For deception technology to generate real intelligence, it must satisfy three requirements:
- Credibility: Is it believable enough that a sophisticated attacker cannot detect it?
- Instrumentation: Can it capture detailed data about attacker behavior, not just basic logs?
- Data exfiltration: Can it retrieve that intelligence securely without giving the trap away?
Traditional honeypots fail at all three. This is why, for much of their history, honeypots were confined to academic research and rarely translated to real enterprise security. The problems were simply too fundamental.
From Basic Honeypots to Advanced Deception: A Different Category
The original honeypots were built as standalone traps. Modern attackers require a far more advanced approach.
CounterCraft’s founders came out of the honeypot world. CEO David Barroso founded the Spanish chapter of the Honeynet Project in 2003, spending years working on open-source deception research alongside the community of practitioners who defined the field. That history is precisely why CounterCraft was built the way it was: to solve the problems honeypots never could.
CounterCraft The Platform creates a dynamic deception environment that behaves like genuine infrastructure across IT, OT, and cloud systems. Rather than waiting passively for an attacker to stumble into a decoy, it builds a credible world for adversaries to move through and, in moving through it, reveal everything.
Key capabilities include:
- Dynamic, Real-Time Response: The platform adapts as attackers interact with the environment. Their actions reveal tactics, techniques, and procedures that defenders can analyze and use to strengthen their security posture.
- Indistinguishable Credibility: High-fidelity digital twins replicate real IT, OT, and cloud systems. These environments behave like genuine assets, making them extremely difficult for attackers to identify as deception.
- Seamless Integration: High-confidence alerts feed directly into SIEM, SOAR, and XDR platforms. Security teams can immediately execute on the intelligence generated by CounterCraft decoys.
- Scalability: Deception assets can be distributed across the environment, giving defenders visibility wherever attackers attempt to operate.
The result is a fundamentally different approach to detection and intelligence, built by people who spent years understanding exactly where honeypots fell short.
Read more about the difference between honeypots and deception here >>>
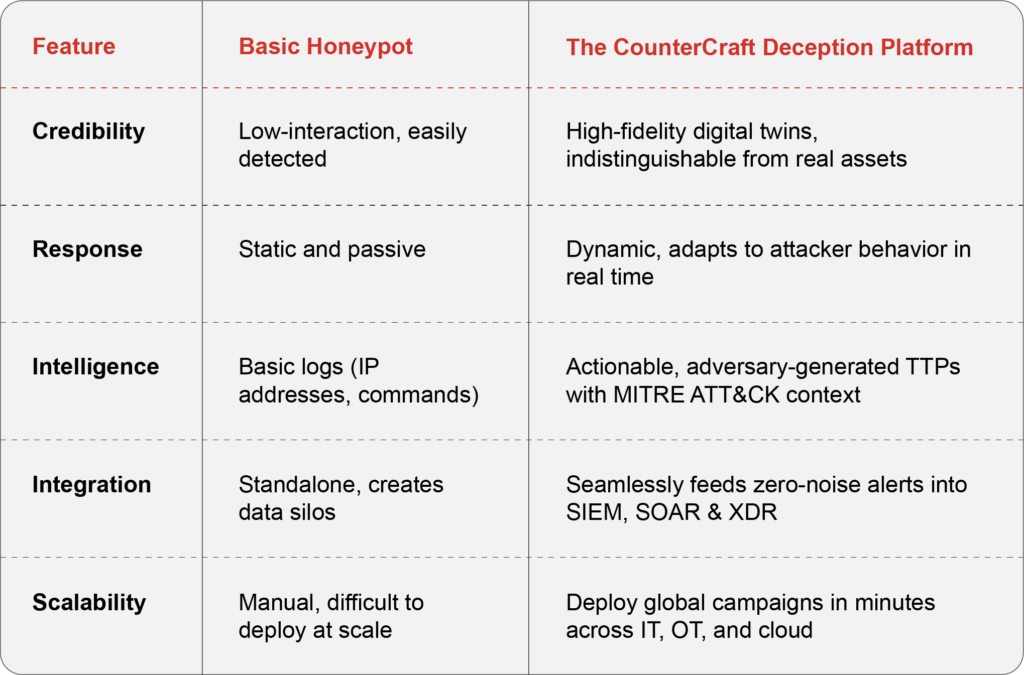
At a Glance: Basic Honeypot vs. CounterCraft
Honeypots opened the door to deception as a defensive strategy, and that contribution matters. But the door they opened leads somewhere far beyond what they were ever capable of delivering.
The organizations that understand this, that see honeypots not as a foundation to build on but as a proof of concept that exposed the need for something better, are the ones investing in deception platforms built for the realities of modern adversaries. That is the space CounterCraft was designed for, by practitioners who spent years inside the honeypot world learning exactly what it could not do.
Interested in seeing how it works? Contact us today.
Key Takeaways
- Like bees to honey – A honeypot is a cybersecurity tool that mimics real systems to attract attackers.
- Detection happens early – When attackers interact with a honeypot, security teams gain visibility into reconnaissance and exploration activity before critical systems are reached.
- Honeypots have limits – Traditional static decoys can be detected, bypassed, or ignored by today’s automated attack tools.
- Advanced threats require advanced deception – Modern deception platforms create credible environments that force adversaries to reveal their tactics and methods.
- Upgrade the strategy – Distributed deception, real-time intelligence, and integration with existing security tools give defenders earlier and more reliable detection.