Edge devices are the most targeted and hardest to monitor entry points in any network, and by the time most organizations know they’ve been compromised, attackers have long since moved on. CounterCraft’s unique deception decoys and deception satellites capture complete attack telemetry from live exploitation attempts, giving security teams fresh IOCs and active C2 infrastructure to work with before production systems are ever touched.
Security teams know edge devices are getting hit. What they don’t know is that by the time a vendor publishes a vulnerability advisory, certain threat groups have already downloaded the patch, reverse-engineered it, written a working exploit, and scanned the entire internet for targets. That window, from public disclosure to active exploitation in the wild, has collapsed from about a month five years ago to under 24 hours today.
Let’s look at a real example. The Citrix advisory from July 18th had attackers in the door by July 20th. Roughly 8,000 vulnerable servers were still exposed a week later, because patching takes time. You have to test, schedule the change, get approvals. Attackers don’t have that problem.
And here’s what makes detection so difficult: the logs these devices generate are nearly useless for identifying exploitation, and sophisticated threat actors know this. They’re not just slipping past your monitoring. They’re deleting whatever thin evidence trail existed in the first place.
So security teams are left trying to piece together what happened on systems that weren’t designed for forensic visibility, working with indicators of compromise extracted weeks after attackers moved on, during cleanup operations rather than active campaigns.
Deception technology offers a different approach…read on to discover how CounterCraft is solving this major issue in a fascinating way.
Campaign 1: Deployed Deception Decoys
The first approach is pretty simple in concept: put real devices on the internet and wait.
Not simulated ones. Actual FortiGate appliances, Citrix gateways, Ivanti MDM systems, real hardware running real firmware, some patched and some not, because that’s what organizational infrastructure actually looks like. When attackers use Shodan to find exposed devices worth hitting, these show up. They’re supposed to. That’s the whole point.
When a zero-day campaign rolls out, these are the devices that get hit. And because they’re built for intelligence collection rather than protecting anything, everything gets captured:
Pre-exploitation telemetry includes the full inbound request content. Every exploitation attempt, including the complete payload, is captured. This provides immediate detection of the initial breach attempt and enables rapid signature creation and IOC development.
Post-exploitation activity is where the real intelligence value emerges. All subsequent communications are captured, revealing what attackers do after successful compromise. Commands executed on the device, data exfiltration attempts, persistence mechanisms, and preparation for lateral movement. Everything is logged and analyzed.
That last part is where most threat intel breaks down. By the time an attack gets written up and shared, the infrastructure has moved and the samples are weeks old. Here, when a decoy gets compromised, the C2 is still live. The malware is fresh. Any organization running the same equipment can take what was just learned and go check their own environment immediately.
The decoy got hit so something real didn’t have to.
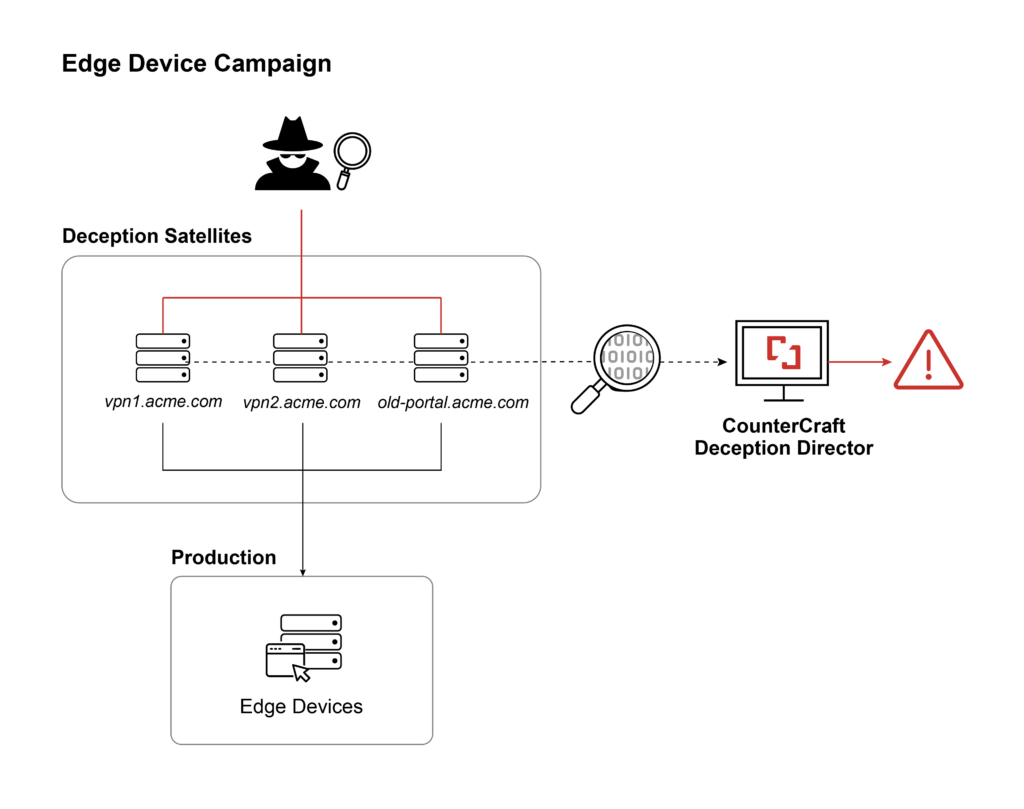
Campaign 2: Deception Satellites
The second approach skips the physical hardware entirely.
Instead of deploying real devices, you deploy what CounterCraft calls Deception Satellites: lightweight gateways that sit in front of your actual edge devices and transparently pass traffic through. If your VPN lives at vpn.bank.com, the satellite lives at vpn1.bank.com. All traffic gets forwarded to the real device. Attackers get authentic responses because they’re actually talking to your production infrastructure. They just don’t know everything is being logged on the way through.
The setup takes under 60 seconds per satellite, and you can deploy as many as you want. One real edge device, dozens of entry points watching for exploitation attempts. When attackers run their enumeration tools, the satellites show up as legitimate infrastructure worth probing. They try something. You see exactly what they tried.
The important detail is who these domains are meant for: nobody internal. They’re not in your documentation. No employee should ever be hitting vpn1.bank.com. So if someone does connect, you already know something interesting is happening. The satellite exists purely to be found by people who are looking for things they shouldn’t be touching.
It’s the same intelligence value as the physical decoy approach, just without the overhead of buying and maintaining hardware. The production device does the work. The satellites do the watching.
Download our one pager to find out more >>>
Rapid Threat Intel
As soon as satellites go live, they start collecting. You don’t have to wait for an incident. The data comes from active exploitation attempts, all of it captured while a campaign is still running, not weeks later. If something similar is hitting your production systems at the same time, you can go check right now, while the threat is live.
If you can install the CounterCraft agent directly on the edge device, you get full visibility into everything before and after exploitation. On Linux-based systems or anything where you control the OS, that’s usually possible.
On hardware appliances like FortiGate, it’s agentless. You still capture all pre-exploitation activity and a meaningful amount of post-exploitation activity, but the ceiling is set by what the device itself logs and what passes back through the compromise channel. HTTP-based post-exploitation gets captured. Some activity outside that channel may not, depending on the device. It’s worth being clear-eyed about that tradeoff. Agentless is still far better than finding out about a compromise three weeks after the fact. It’s just not the same as full agent-based collection.
Running Multiple Campaigns at Scale
At organizational scale, you don’t run one deception environment covering everything. You run separate campaigns for separate contexts: one per agency, data center, OT segment, or cloud tenant. Each generates its own clean telemetry, mapped to the right environment. When a satellite catches something, you know exactly where it was targeting and what it was going after.
This also means campaigns can be tuned differently. One might focus on VPN exploits. Another might validate whether a patch actually closes the vulnerability it claims to close. A third might watch for lateral movement from an insider threat angle. Keeping them separate keeps the signal clean and the attribution precise.
Security That Actually Works with Edge Devices
Edge devices create a particular kind of problem. This approach addresses the most difficult points of edge device protection.
- No production impact. Satellites and decoys don’t touch your production edge devices except as transparent pass-through. Your actual VPNs, firewalls, and gateways keep running normally. No performance hit, no added latency, no risk of breaking connectivity for the people who depend on them.
- Failures stay contained. If one campaign gets noisy or an attacker figures out they’ve hit a deception system, it doesn’t expose anything real. Other collection efforts keep running. Production infrastructure stays untouched.
- Attribution gets cleaner. Because campaigns are segmented, when you know which satellite was hit and with what technique, you can map that activity to MITRE ATT&CK and build a picture of what a specific threat actor is actually doing, in this very moment.
- Compliance evidence comes built in. Each environment generates its own telemetry that can be mapped to NIST 800-53 or whatever framework applies. The logs are comprehensive, the evidence is preserved, and the chain of custody is intact if you ever need it.
Edge Device Protection in Action
One financial institution deployed satellites and detected reconnaissance against their edge devices within hours of a new exploit going public. Their production systems were never touched. Their security team had IOCs before most organizations had finished reading the advisory.
That’s the consistent pattern. Security teams know that edge device compromises happen. The question is whether you find out during the attack or after. Running deception infrastructure against your edge devices means that when a mass exploitation campaign launches, you already have samples, you already have C2 infrastructure, and you already know what the attack looks like in practice. You can check your production systems against real indicators while the campaign is still active.
Traditional detection tells you that you were compromised. This tells you that devices like yours are being targeted right now, and here’s exactly how. If you’re interested in finding out more, just get in touch.