Late last year, US President Joe Biden signed the National Defense Authorization Act for Fiscal Year 2023 into law, allotting $816.7 billion to the Department of Defense. This includes $44 million to Cyber Command for “hunt forward” missions, part of the command’s strategy for “persistent engagement,” defined as the need to constantly and speedily interact with adversaries in cyberspace.
The Act authorizes fiscal year appropriations for the Department of Defense, Department of Energy national security programs, Department of State, Department of Homeland Security, and the intelligence community.
From a proactive digital standpoint, what the 2023 NDAA really does is reinforce USCYBERCOM’s persistent engagement and defend forward strategy. I have seen firsthand how U.S. networks are under constant assault from adversary nations and malicious cyber actors seeking to exploit vulnerabilities and disrupt U.S. society and military capabilities. The Act includes critical authorities to support US national defense, foreign affairs, and homeland security.
Active defense and deception technology in the 2023 National Defense Authorization Act
The act explicitly mentions active defense and deception technology, cementing their importance in the global cybersecurity landscape. The act states:
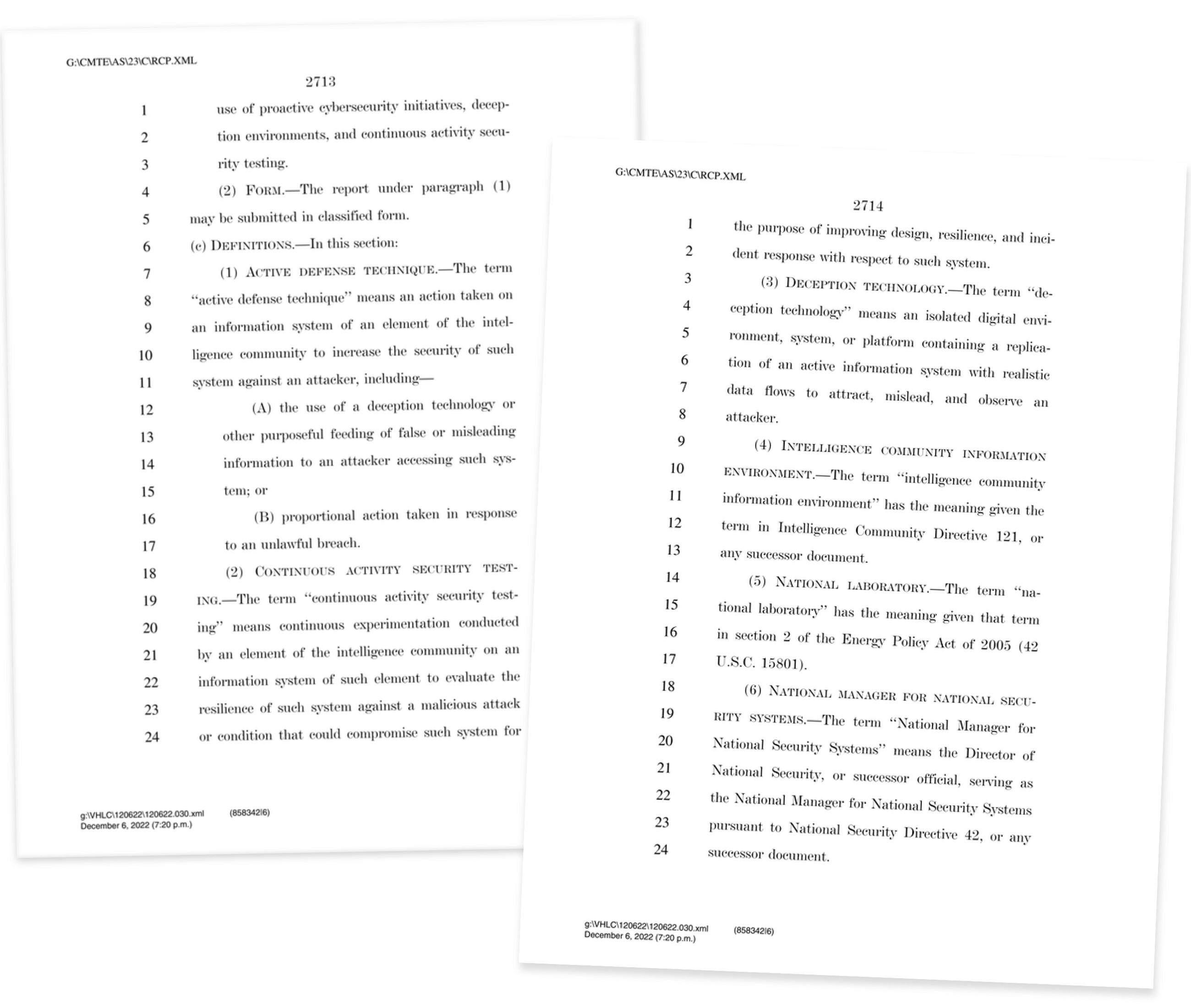
“Not later than 1 year after the date of the enactment of this Act, the Chief Information Officer of the Intelligence Community shall conduct a survey of each element of the intelligence community on the use by that element of proactive cybersecurity initiatives, continuous activity security testing, and active defense techniques.”
The 2023 National Defense Authorization Act
Here is the excerpt from the act that mentions active defense and deception technology:
- SEC. 6320. PROACTIVE CYBERSECURITY.
- ACTIVE DEFENSE TECHNIQUE—The term ‘‘active defense technique’’ means an action taken on an information system of an element of the intelligence community to increase the security of such system against an attacker, including—
- (A) the use of a deception technology or other purposeful feeding of false or misleading information to an attacker accessing such system; or
- (B) proportional action taken in response to an unlawful breach
- DECEPTION TECHNOLOGY—The term ‘‘deception technology’’ means an isolated digital environment, system, or platform containing a replication of an active information system with realistic data flows to attract, mislead, and observe an attacker.
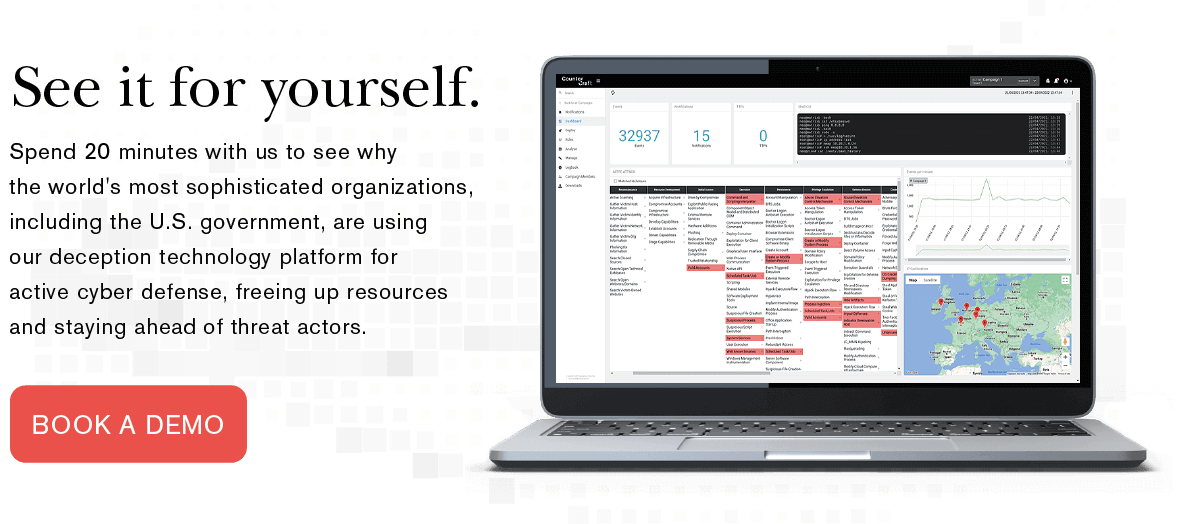
CounterCraft has the ability to provide real-world, actionable intelligence to support the defense department in advanced cyber operations such as the ones highlighted in the 2023 National Defense Authorization Act.. In addition, we currently have a $26 million sole-source contract with the U.S. Government to support advanced cyber operations such as the ones highlighted in the 2023 National Defense Authorization Act.

Strengthening the Department of Defense’s cybersecurity strategy and capabilities are the priorities, and the need for and use of techniques like deception mentioned make it clear that governments are betting on proactive cyber defense solutions.
Hunt-forward operations engage adversaries in cyberspace in order to disrupt cyber threats, degrade the capabilities and networks of adversaries, and continuously harden the Department of Defense Information Network (DODIN). The proactive cyber operation requires operating as close to the origin of adversary activity as possible, increasing the reach of U.S. cyber operators and neutralizing the threat at its source.
Active defense is the best way to gather actionable intelligence, which can then be shared to bolster homeland and network defense while exposing adversary tactics, techniques, and procedures before they can be used against the United States.
As Senate Armed Services Committee Chairman Jack Reed (D-RI) said, this bill only serves to strengthen our national security, making sure the military has what it needs to “defend our nation, deter conflict, and meet a range of evolving security challenges.”
Defending the nation with world-class deception technology
The Department of Defense highlighting proactive defense and deception techniques shows their energetic ambition to learn new ways to detect attacks, collect threat intel and change adversarial behavior. We urge all government and critical infrastructure cybersecurity teams to contact us to Learn more about how we can quickly upscale your active defense and deception tooling.

Born from the GCHQ Accelerator, backed by In-Q-Tel, tested by the Defense Innovation Unit, and trusted by the US Air Force, CounterCraft provides the best threat detection capabilities to defend against nation-state cyber adversaries. We have a $26 million contract from the U.S. Government to support advanced cyber operations such as the ones highlighted in the 2023 National Defense Authorization Act.
With an established track record of national security deployments our cyber threat detection platform allows national defense and security organizations to detect, investigate and disrupt advanced cyber threats on internal and external facing networks faster than ever before. Get in touch to discuss our solutions or to book a demo.

Dan Brett is a founder and CPO of CounterCraft. You can find him on LinkedIn.