MITRE has recently released the Engage v0.9 Beta version. In MITRE’s words, “MITRE Engage is a framework for discussing and planning adversary engagement, deception, and denial activities. Engage is informed by adversary behavior observed in the real world and is intended to drive strategic cyber outcomes. Engage was created to help the private sector, government, and vendor communities to plan and execute the use of adversary engagement strategies and technologies.”
MITRE Engage replaces the MITRE Shield knowledge base, focusing on the areas of denial, deception, and adversary engagement. It is a streamlined version, based on technical feedback from the entire cyber community. Engage is wholly focused on strategic planning and analysis within the framework of denial, deception, and adversary engagement, in an effort to create more meaningful results from the MITRE knowledge base.
We were fans of the MITRE Shield approach, but now we are even bigger fans of MITRE Engage!
Making the change to Shield is a good idea for several reasons:
– Keeps focus on strategic planning
– Categorization of technique has been streamlined and revised to focus on defender strategy
– Upcoming introduction of References, which will be a community-curated selection of real-world examples of Activity implementations
– The new concept of Adversary Vulnerabilities, which allows defenders to zone in on points of weakness to have maximum impact
Even though MITRE Engage is still in beta and waiting for the release of the V1 version, we love it so much that we decided to start integrating Engage with our Cyber Deception Platform. It’s a great time to start using Engage, as MITRE is welcoming any feedback about this v0.9 Beta release. Anyone can contact them with suggestions or ideas on how to improve Engage.

What is MITRE Engage?
MITRE Engage is organized around goals, approaches and activities.
Goals are the big objective you would like to accomplish. Selecting a goal should be the first step in any adversary engagement operation. Once you have selected your goal, all other activities should be selected to drive progress towards that goal.
Strategic Goals
| Name | Description | ID |
|---|---|---|
| Prepare | Help the defender think about what they want to accomplish with operations. | SGO0001 |
| Understand | Make sure that the defender is capturing, utilizing, and refining knowledge learned to improve the defender’s posture. | SGO0002 |

Engagement Goals
| Name | Description | ID |
|---|---|---|
| Expose | Reveal the presence of ongoing adversary operations. | EGO0001 |
| Affect | Negatively impact the adversaries operations. | EGO0002 |
| Elicit | Learn about adversaries tactics, techniques, and procedures. | EGO0003 |

Approaches are the plans you select to progress towards achieving your big objectives, and can be either strategic or engagement approaches.
Strategic approaches help you to focus on the steps you must complete before, during, and after an operation to ensure that your activities are aligned with your overall strategy. Strategic approaches help ensure that your operations of today inform your operations of tomorrow.
Engagement approaches help you to identify what actions you would like to take against your adversary and help you to drive progress towards that impact.

Strategic approaches
The migration to Engage brings some of the missing steps that weren’t present in SHIELD. The situation was similar when the ATT&CK team included the PRE-ATT&CK tactics and techniques some time ago. You can be engaging with your adversaries but there is a lot of going on in the preparation and analysis phases. And this is where the strategic approaches fit really well.
For the preparation phase, MITRE has included the PLANNING strategic approach (SAP0001), that includes the following activities:
| Define Exit Criteria | Define the set of events that would lead to the unnegotiable conclusion to the operation. | SAC0005 |
| Develop Threat Model | Identify, understand, and prioritize potential engagement targets. | SAC0004 |
| Persona Creation | Plan and create a fictitious human user through a combination of planted data and revealed behavior patterns in support of your strategic objectives. | SAC0002 |
| Strategic Goal | Define the objective of the desired end-state of your adversary engagement operations. | SAC0001 |
| Storyboarding | Plan and create the deception story. |

Whenever you are planning a deception campaign, you should start planning what you want to achieve. Deception is just not deploying some decoys and breadcrumbs and seeing what happens.
One of the most important activities in this phase is the definition of an exit criteria once you have completed your goals. For example, if your goal is to find out the intentions of a specific threat actor, or collect all the TTPs, you should have planned how you are going to have a credible end of the attack path. Credibility is key, and that is also why the Persona Creation or the Storyboarding are also critical in your mission.
The other strategic approach takes place at the end of your deception campaign: Analysis (SAP0002). It’s time to understand what happened in the deception campaign, and make the information actionable. Analysis included the following activities:
| Distill Intelligence | Turn raw data gained during an operation into actionable intelligence. | SAC0008 |
| Hotwash | Review the retrospective of operational activities. | SAC0006 |
| Inform Threat Model | Update existing threat models based on intelligence gained during engagement operation. | SAC0009 |
| Refine Operation Activities | Update and improve the implementation of operational activities to better achieve the strategic goal. | SAC0007 |

Turning all the raw data into actionable intelligence should be the priority in this phase. And the sooner we can automate the use of that actionable intelligence the better. It is desirable to have integrations with other security products like SOAR, SIEMs, EDR, etc. that can use this intelligence in real time.
And finally, similar to the OODA loop, we need to refine our Planning activities based on the feedback from the results.

MITRE Engage in CounterCraft’s Deception Director
CounterCraft’s Deception Director is an active defense platform that helps in the design, deployment and monitoring of deception campaigns. Those campaigns can be considered as a set of different Engage approaches and activities.
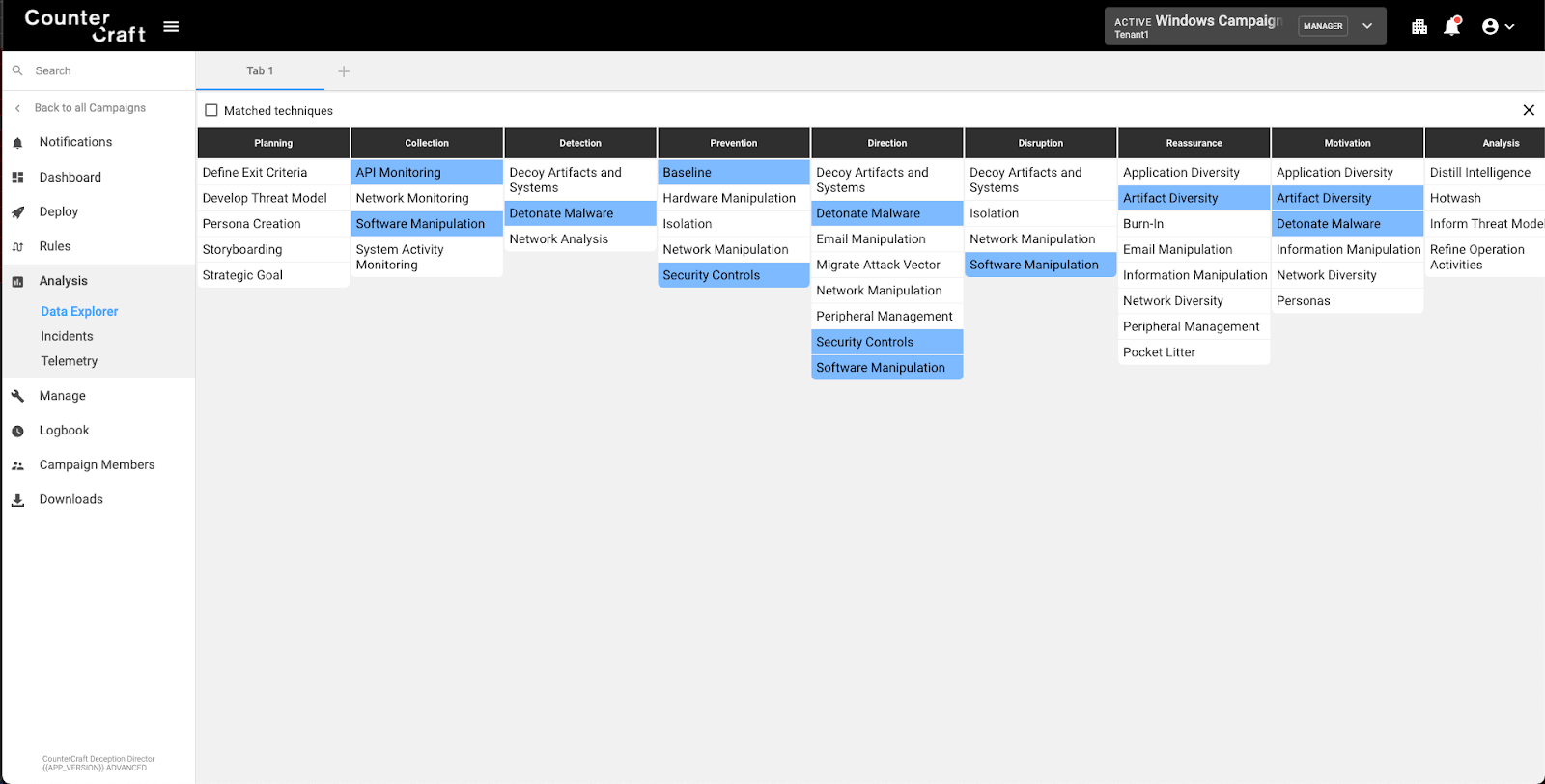
We have added the Engage matrix in different places of the application so that we can show which approaches and activities are covered.

Threat Actor Database
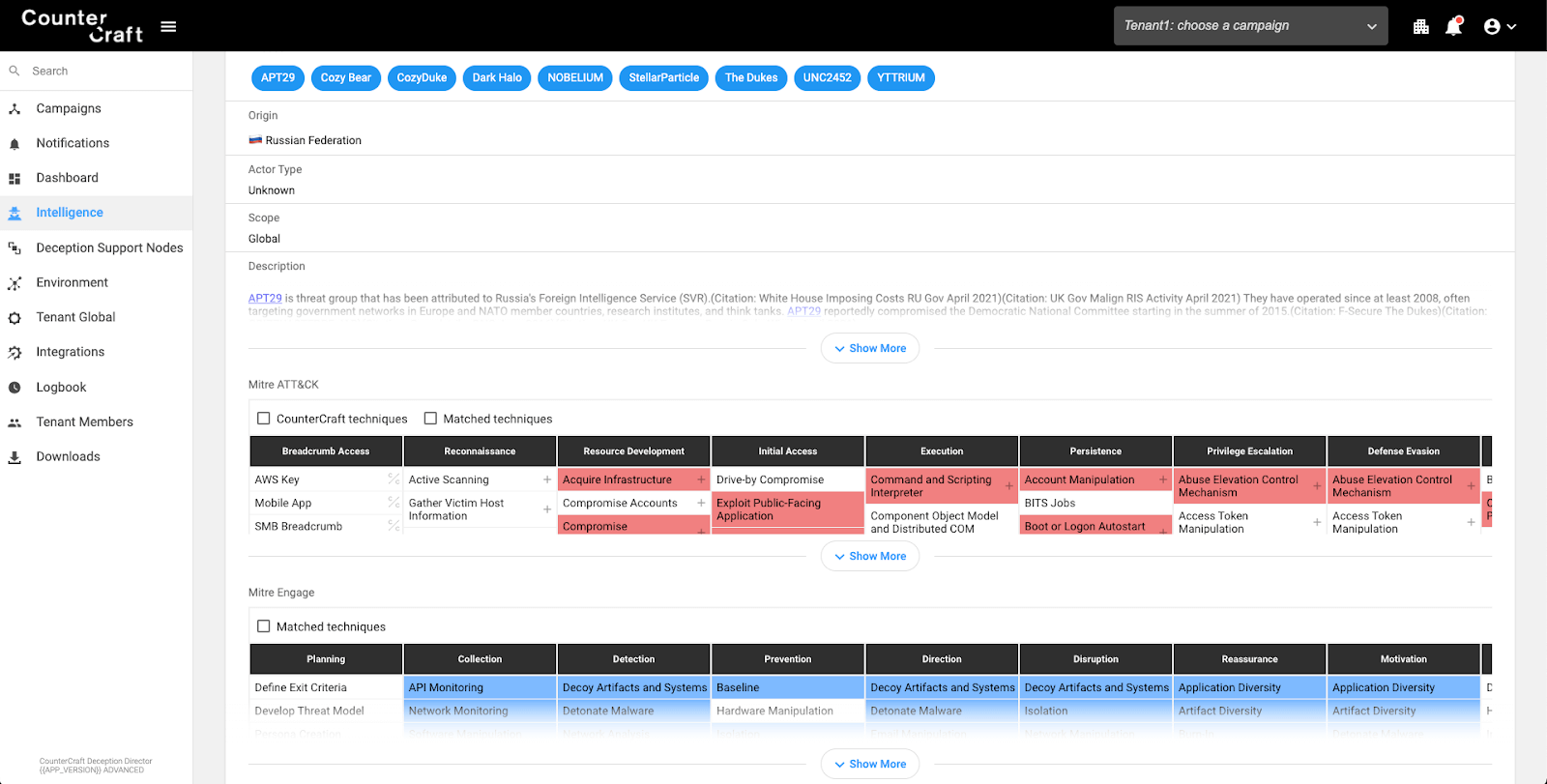
We could start having a look at our threat actor, in order to know which ATT&CK TTPs they use, and which Engage approaches and activities could be used against them. We can use the ATT&CK mapping provided by Engage in order to select the techniques that can be used by the blue team against this specific threat actor.
In this screenshot you can see our threat actor information database showing the ATT&CK Matrix (Red) associated with the threat actor and the Engage matrix (Blue) highlighting specific defensive activities that would apply to this actor.

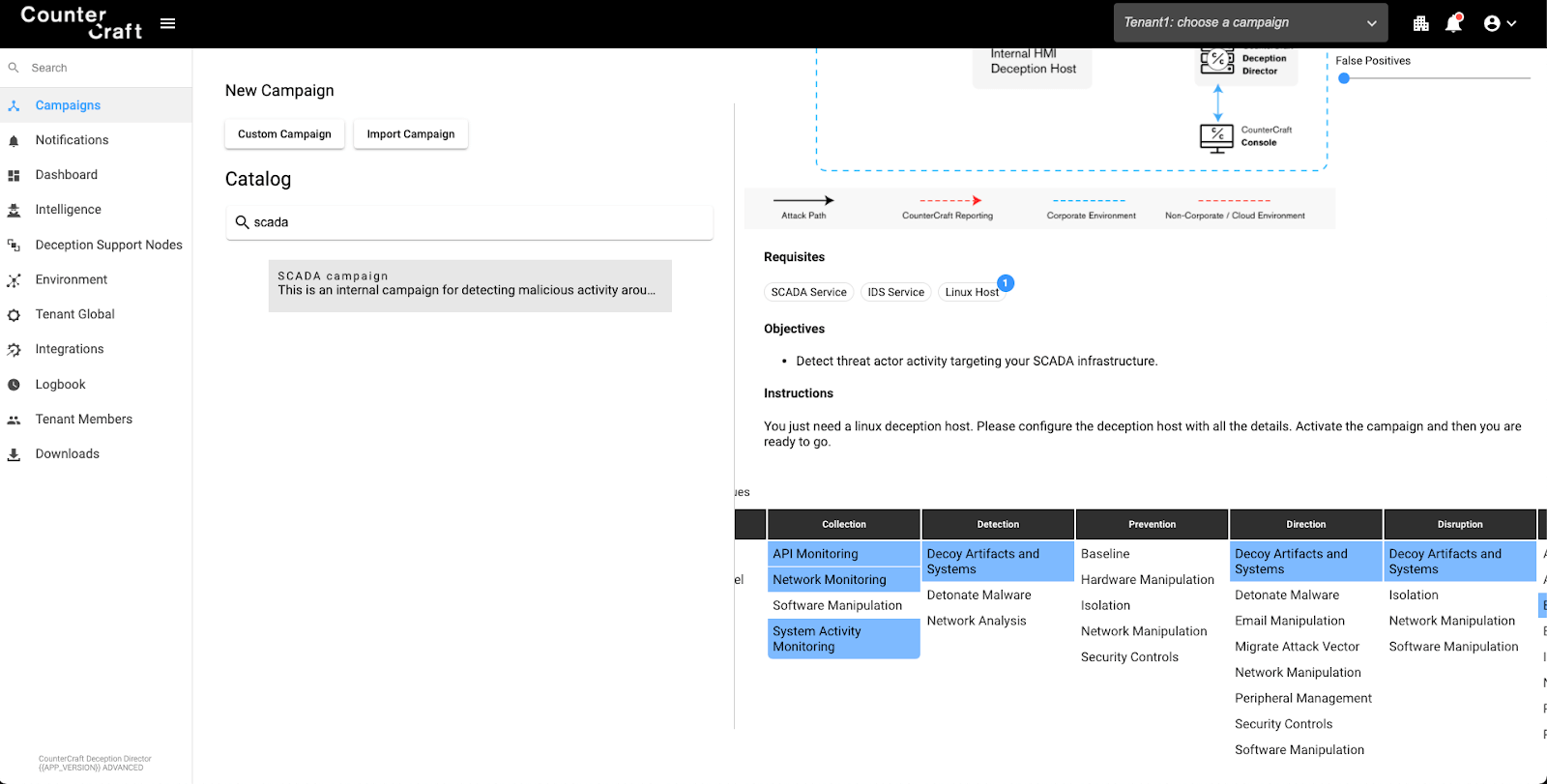
Campaign Catalogue
Once we have checked the Engage approaches that we should use, then we can choose any campaign from our catalogue that fits with those approaches and activities. The Campaign Catalogue provides ready made campaigns to start you on an active defense journey using CounterCraft.

Campaign Builder
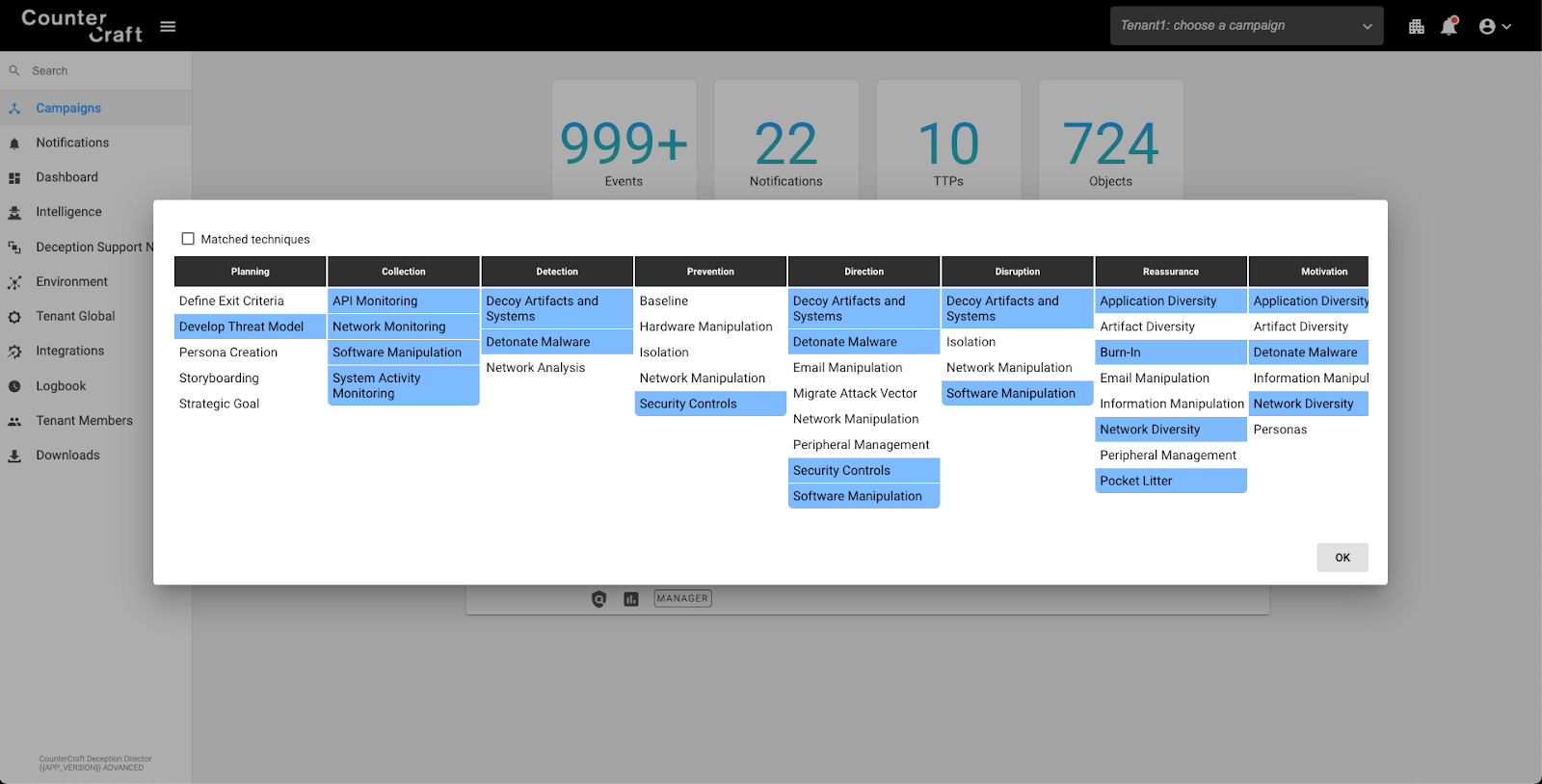
We can then add deception hosts, services or breadcrumbs to our fresh new campaign that will include new Engage activities, depending on the type of the asset.
This screenshot shows all the Engage approaches and activities that are facilitated by the current campaign, useful for checking that your campaign is covering the defensive areas you need.

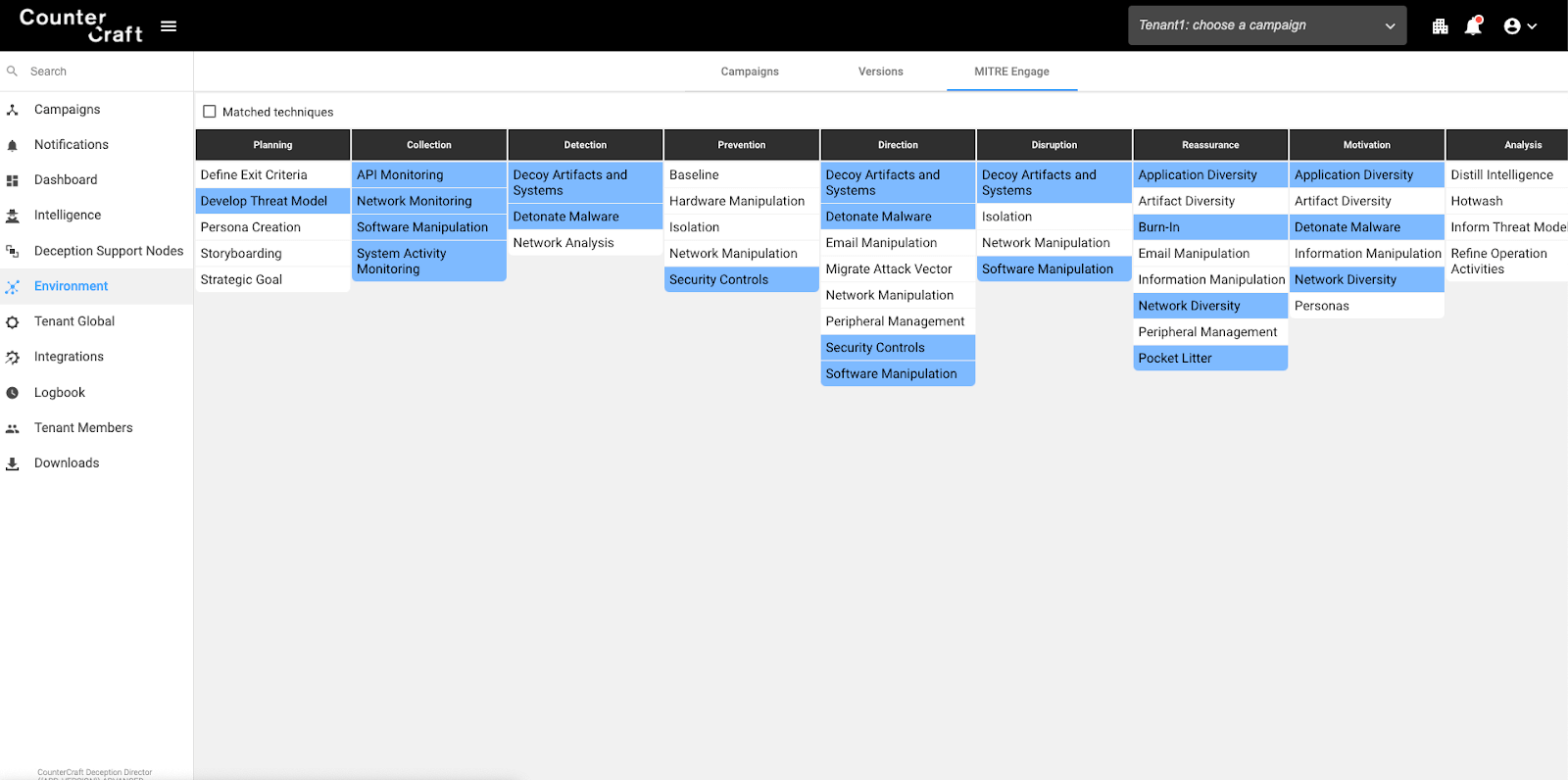
Deception Environment
Now we can have a look at all the Engage approaches and activities covered by all our deployed campaigns. CounterCraft allows you to deploy more than one campaign at a time so you can defend against different adversaries and threats (internal and external) at the same time.

Data Explorer
When we integrated MITRE ATT&CK in our data explorer (that is getting all the events from the campaign) it was a great feature that helped to visualize all the TTPs originated in the campaigns.
Now, thanks to the ATT&CK -> Engage mappings, we can map all the ATT&CK TTPs detected into Engage activities.
This is like a real-time map of what you should be doing to defend against attacks in progress. CounterCraft detects attacks and collects intel. The intel is processed and enriched to give you IOCs and further insight such as these defensive recommendations.

Summary
As we have seen in this blog post, the release of MITRE Engage is a fantastic opportunity to improve our active defense strategies. Active defense ranges from basic cyber defensive capabilities to cyber deception and adversary engagement operations. The combination of these defenses allows an organization to not only counter current attacks but also to Learn more about that adversary and better prepare for new attacks in the future.
