What is deception technology?
Deception technology is a type of cybersecurity that uses deceptive tactics, from fake network environments to honeypots and breadcrumbs like bogus credentials, to catch malicious actors and learn more about them.

The benefits of deception technology.
-
1 Detect attackers before there is a breach
With deception, you can find attackers and observe their movements before they have even entered your network.
-
2 No need to disrupt regular network function
Deception technology can work without touching your network systems, meaning minimum disruption to normal processes and business flow.
-
3 Eliminate false positives
Deception creates environments and data that, by definition, should not be entered or touched. That means there is an almost total reduction of false positives, noise, and dead-end alerts.
-
4 Scale easily
Deception can scale easily and be automated for maximum efficacy even as your organization grows and changes.
-
5 Gain threat intel specific to your organization and in real time
Deception technology doesn’t rely on generic threat intel feeds—it creates threat intel by engaging attackers, and delivers it to your security team in real time.
-
6 Works across many types of systems
Legacy system? No problem. IoT devices to protect? Deception works on those too. Cyber deception is versatile and adaptable.
Organizations today face more daily cyber attacks than ever, and the stakes (both financial and otherwise) get higher and higher. These attacks are designed by adversaries to disrupt businesses or strategic missions and carried out using an evolving set of Tactics, Techniques and Procedures (TTPs).
Defenders continually feel that they are at a disadvantage as they need to protect their assets all the time, and in organizations which no longer have classical boundaries or perimeters, and who are adopting new technologies, business models and global partnerships at a faster rate than ever before. It’s snowballing out of control.
For the past 30 years enterprise Chief Information Security Officers and their Enterprise Security Architects, if they existed, bought and built solutions which were all about “keeping the bad guys out” in a very overt and straightforward manner, and the industry evolved through the vocabulary of IDS, IPS, Firewalls, Cryptos, Anti-virus, Security Information & Event Management (SIEM), Cyber Threat Intelligence, Cloud Access Security Brokers, Security Automation & Orchestration.
All of these technologies and approaches still deliver value and should keep about 80% of the attackers out.
What of that other estimated 20%?
Deception tools and techniques are being used more and more often to proactively protect important information assets and systems, and divert persistent adversaries to synthetic environments which engage to gather direct threat intelligence, keep them occupied and misdirect them through deception campaigns.
This is where the value of cyber deception really comes into its own as it enables defenders to design, build and operate synthetic and fake environments that fool the attackers into thinking they are accessing real production environments. As a result, they give away details of their Tactics, Techniques and Procedures (TTPs).
With this information it is possible to carry out a number of valuable defense-enhancing activities at different levels of an organization.
For example

The CISO can get detailed intelligence on real attackers and what they are interested in accessing in the business. They can use this to inform future defense posture and investments, and talk to the board and peer C-Suite executives, before any breach occurs.

Enterprise Security Architects can deploy deception to improve the protection of certain information assets – the crown jewels.

Real-time information from a deception environment can be integrated machine-to-machine in a Security Operations Centre with SIEM and Threat Intelligence Platforms to enhance triage and threat hunting disciplines.

As bad guys waste their time in fake environments, not only are your real networks safe, they may be deterred as their effort has been increased massively.
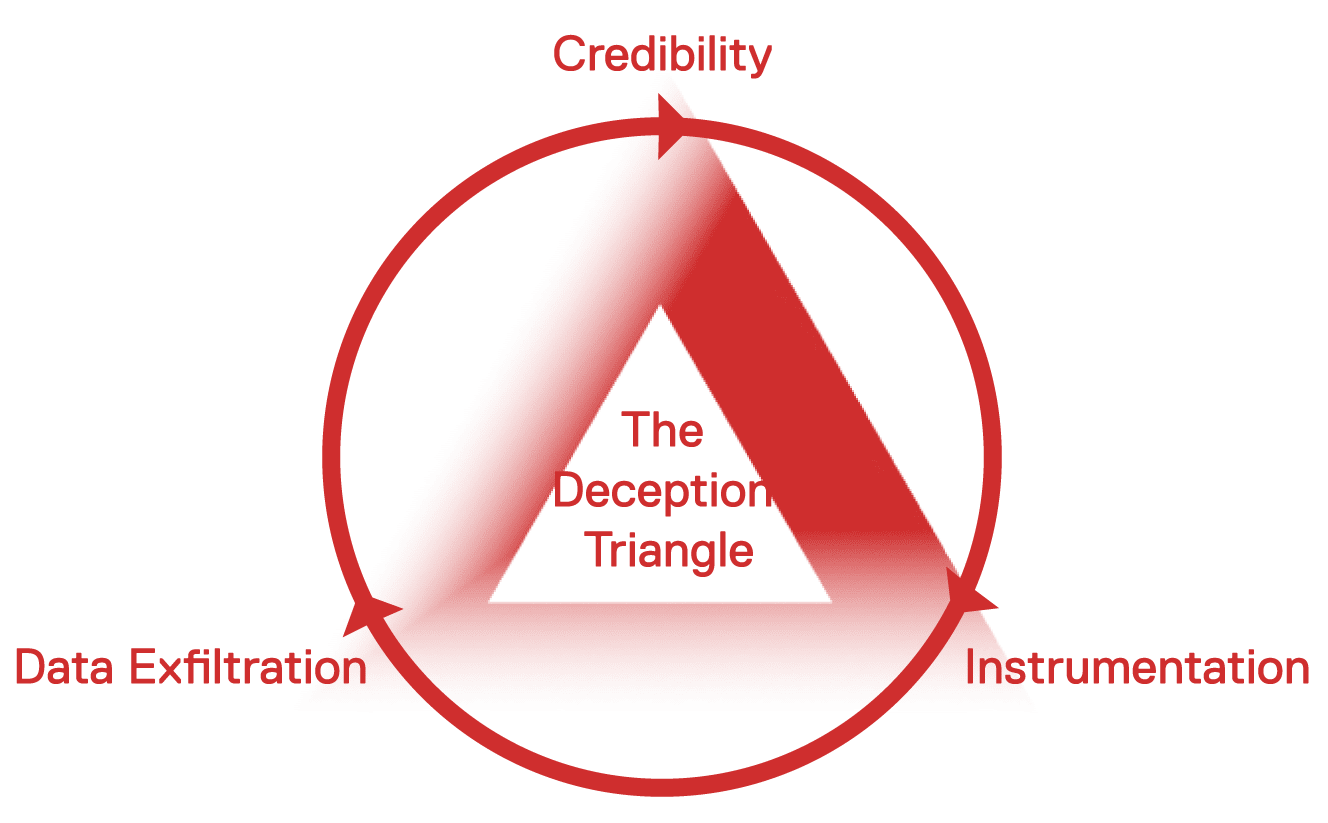
The three pillars necessary for effective deception technology are:
1) Credibility: Is it believable?
2) Instrumentation / Telemetry: Are you able to gather deep data about what people are doing on the system?
3) Data Exfiltration: Are you able to bring that data home without revealing yourself, so you can do something about it?

What attacks can deception technology detect?
Deception technology can detect many different types of attacks, including attacks that other security measures miss. Deception technology is especially effective at detecting lateral movement and insider threat, as well as advanced, targeted attacks.
-
VPN
-
Credential theft
-
Lateral movement
The state of deception technology today
Deception technology is still in its youth.
First-to-market deception technologies solved the data gathering issue but still have important credibility issues, making them not ideal for complex systems and high-stake networks.
CounterCraft The Platform has real IT and ActiveBehavior technology, a revolutionary way to keep honeypots and breadcrumbs from going stale. We have solved the deep data problem, thanks to a kernel-level implant that observes the actions of the adversary, which is stealthed to avoid detection. And, to top it off, we have a very well-engineered command and control infrastructure, ActiveLink, for bringing the data home in a secure and stealth way, meaning we do not give away our presence to an adversary.
The future of deception lies in a fourth axis on the deception triangle: the dynamic response. A dynamic response capability allows you to shift and manipulate the environment to extract more information from your adversaries than they would normally leave.The future of deception technology is here, and it is dynamically shaping the deception environment to elicit changes in adversary behavior and better threat intel gathering.
Hiding the truth from attackers, which relies on the following techniques:
Masking: Masking mechanisms operate by making the truth unable to be detected.
Repackaging: Repackaging mechanisms operate by mak- ing the truth appear to be something else.
Dazzling: Dazzling mechanisms operate by making the truth difficult to be distinguished from false information.1
And presenting false information as truth to attackers, which uses the following techniques:
Mimicking: Mimicking mechanisms operate by having the deceiver portray the false information in such a way that it appears to be the truth.
Inventing: Inventing mechanisms operate by creating entirely new information that appears to be truthful.
Decoying: Decoying mechanisms operate by attracting the adversaries’ attention away from the truth.
Check out some real-world use cases


Financial services & banking
Safeguarding financial transactions, customer data, and market stability.
Learn more

Government
Defending against foreign interference, securing sensitive information, and maintaining national security.
Learn moreIs my business mature enough for deception?
Who can use cyber deception?
We get this question all the time. Deception technology is gaining recognition as one of the most fail-proof ways to protect against cyber attackers, and one of the only ways to detect insider threats and lateral movement. When we are approached by businesses who are interested, one of their first questions is “Am I mature enough for deception technology?”
We’ve created a free resource to help answer that very question. Our free e-book “Are You Ready for Deception Technology?” features nine pages of the valuable advice we give to organizations that approach us looking to improve their cybersecurity posture. The ebook also includes a simple quiz that will guide you to next steps.
Download now
Find out how The Platform addresses the key challenges in your organization including insider threat, lateral movement, ransomware, and talent gap mitigation.
View use cases