What you’ll learn
How we capture attacker behavior that traditional sandboxes miss
How you can observe complete attack chains, lateral movement, and more
Finding out in real-time how your defenses would have performed
Additional Resources
Frequently Asked Questions FAQS
Traditional sandboxes analyze the malware file itself: what processes it spawns, what network connections it makes. CounterCraft captures what the human attacker does after the malware runs, including their reconnaissance, lateral movement, data targeting, and complete attack methodology. This secondary human activity is what determines if an attack succeeds, and it’s what standard sandboxes cannot see.
Sophisticated attackers check for sandbox environments before deploying their real tools. When they encounter realistic services, authentic credentials, and believable data pathways, they think they’ve successfully compromised a real network. This draws them deeper and reveals their complete playbook: the tools, techniques, and objectives that static sandboxes miss entirely.
As long as needed, up to days or weeks if necessary. Sophisticated threats often wait to deploy their actual attack tools, and we can safely observe for extended periods to capture their complete methodology. Many customers keep attackers engaged for 24-48 hours while simultaneously securing their real network.
The digital twin is completely isolated with strict access controls and continuous monitoring. All security controls are aligned to incident response standards with comprehensive evidence handling.
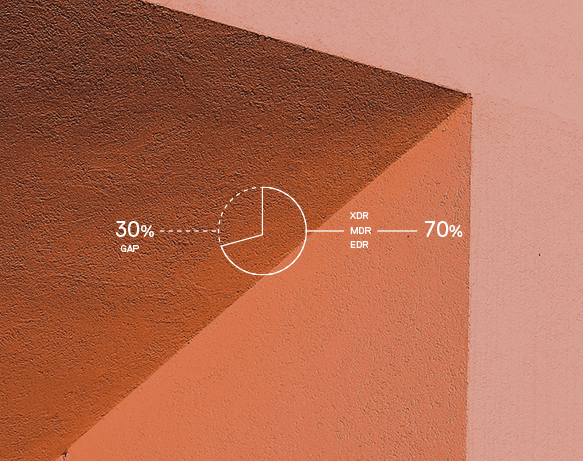
Outputs map to MITRE ATT&CK, route to SIEM, XDR, SOAR, and a threat intelligence platform, and include actions that reduce dwell time and improve decision quality.
All findings automatically map to MITRE ATT&CK and route to your SIEM, XDR, SOAR, threat intelligence platform, and case management tools. This reduces false positives, speeds threat hunting, and improves decision quality across your security stack.
Yes. The realistic environment is specifically designed to engage APT-level adversaries who use staged payloads and sophisticated evasion techniques. Capturing their tradecraft generates the highest-value threat intelligence for raising organizational readiness and informing control tuning.
Standard automated sandboxes are excellent at what they do: quickly identifying if files are malicious. But they’re designed for speed and automation, not for understanding sophisticated human adversaries. CounterCraft is the gold standard when you need intelligence about what advanced attackers actually do: the human behavior that happens after the initial malware runs. The secondary activity that determines whether an attack succeeds or fails.
Track precision rate improvements, reduced MTTD and MTTR, false positives eliminated, analyst hours saved, and expanded ATT&CK coverage. Most customers see immediate value in the specific, actionable intelligence that feeds directly into defensive improvements.