Financial services is one of the most targeted industries today, bombarded with ransomware and phishing attacks daily. 74% of financial institutions experienced a rise in cyber crime over 2020 and 20211, with the average cost of a data breach in the financial sector totaling $5.72 million2.
Growing cyber fraud, a mobile attack surface, the emergence of cryptocurrency, and a move toward third-party payment partners—all create new cybersecurity challenges that demand powerful, flexible defense with deep visibility and minimal management. Traditional cybersecurity is not enough to mitigate risk and protect financial institutions. Deception technology makes it possible to take a proactive cybersecurity stance.
We’ve created a full data sheet on how deception technology can improve the security posture of financial services that you can download here. Read more about the specific challenges and our solution below.
The Specific Challenges of Financial Services
The financial sector is made up of very high-value targets, which is one of the biggest challenges faced when protecting it. The stakes are high, and therefore the attacks tend to be more sophisticated.
- Banks and financial institutions are a major target of both ransomware and phishing attacks because of their monetary value and transactions.
- Identity and financial fraud are rampant.
- Critical payment systems (such as SWIFT) are complex and high stakes.
- Financial organizations have limited cycles because they are always defending against something, making innovation difficult.
As these high-value networks are ever more vulnerable to attack, it is vital to find new security solutions. Deception technologies can be used to provide an extra dimension of security to banking and financial services networks. With deception, it is possible to detect malicious activity, collect valuable threat intel and also create and respond to adversary activity in real time.

All of this is achieved with zero impact on existing systems, and zero risk to business continuity. This is a major plus for financial services organizations, which often have complex systems that cannot be touched.
Example Deception Campaign for Financial Services
Here is a real-life example of how deception has worked to protect an important aspect of financial services —SWIFT networks. This campaign allows organizations to track the data that the adversary is interested in as well as how they are trying to get it.
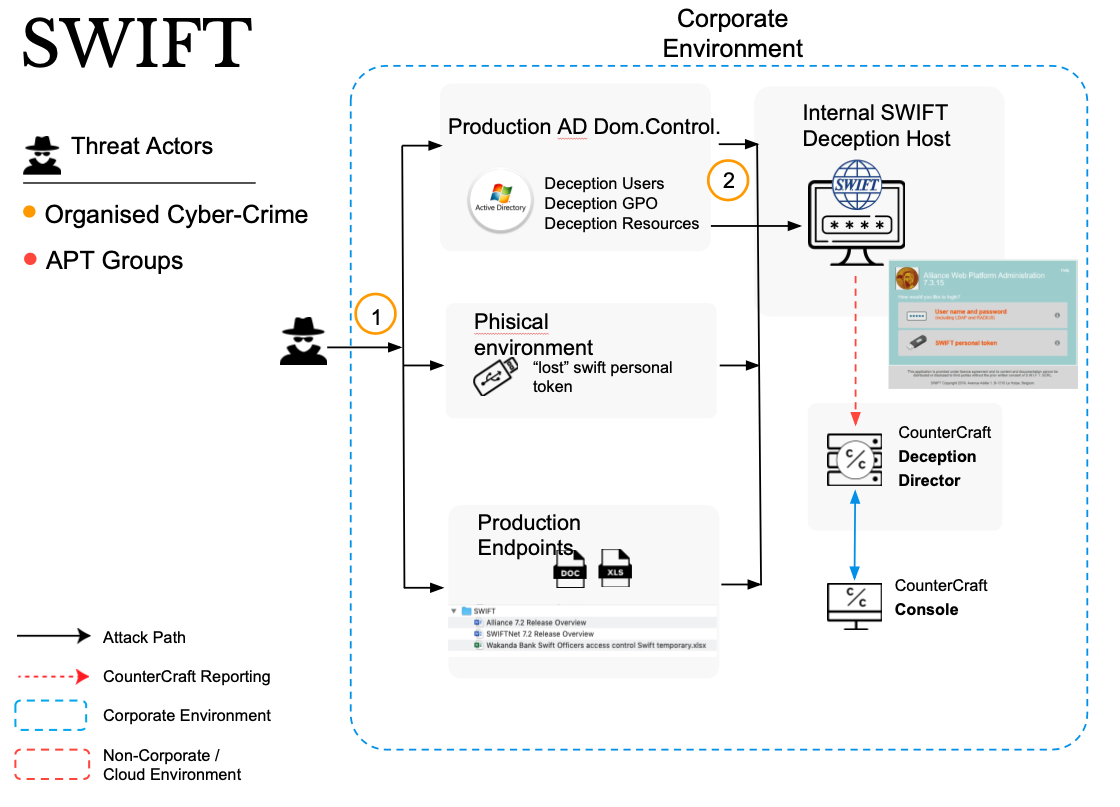
- In Phase 1 of this campaign, the attacker tries to enter the production environment via an Active Directory domain controller.
- In this environment, the attacker finds decoy users, decoy GPOs (Group Policy Objects) and other deception decoys.
- The attacker accesses an internal deception host that simulates a SWIFT network. It reports every move of the attacker to the deception director, who can manage the attacker’s movements via the console.
THE RESULT
The compromise of a SWIFT network and the subsequent misuse of funds and transfers was successfully avoided.
Benefits
Deception can help in the proactive protection of high-value targets without imposing any burden on the normal operation of services.
- Actionable threat intelligence with zero false positives tailored to your organization Intuitive platform requiring minimal technical resources to manage
- Flexible deployment model that includes on premise within the network, on premise outside the network, and in any Cloud Service Provider environment
- No emulations and no complicated physical and/or virtual appliances. We install on real unallocated/nonproduction physical or virtual systems
- Truly mimic your production environment by deploying the necessary servers, endpoints, applications, and services required
- Real-time telemetry, Indicators of Comprise (IOCs), and Techniques, Tactics, and Procedures (TTPs)
- Automatically map threat intelligence to the native MITRE ATT&CK Framework integration within the platform
- Protects your current investments by integrating with existing solutions
To Learn more about how deception is uniquely positioned to protect financial services, download the full data sheet here.
For more examples of how deception has prevented cyber attacks and to Learn more about CounterCraft, contact us.
1https://www.businesswire.com/news/home/20210428005365/en/COVID-Cyber-Crime-74-of-Financial-Institutions-Experience-Significant-Spike-in-Threats-Linked-To-COVID-19 2https://www.upguard.com/blog/cost-of-data-breach