Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
Categories: Company News
We welcome our new strategic advisor, Kevin Rogers. Kevin Rogers is the Founder and Managing Partner of Cyber Advisory Partners (CAP) LLC, and he has had a long career in federal and government sectors Read more

-
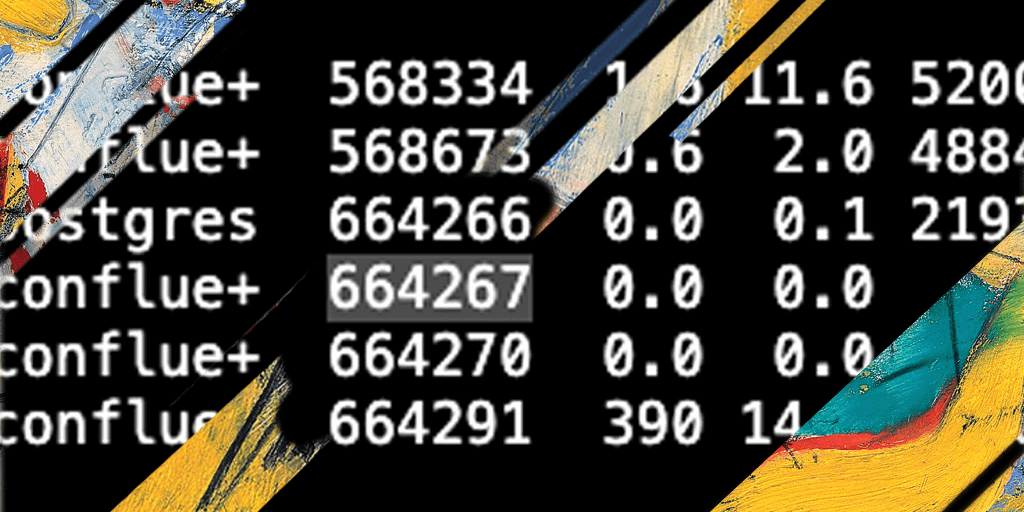
In this post, we focus on ‘Cetus’, a worm that compromises open Docker daemons with two goals: cryptocurrency mining, and to propagate itself. Read on. Read more

-
Categories: Company News
The founders of CounterCraft talk about the threat actors they are finding and classifying among internet noise using deception machines. Watch the video. Read more
-
We have described different payloads that we were observing related to the exploitation of CVE-2021-26084. The majority of the incidents were trying to install crypto miners. Read on as we describe a successful exploit that installs a cryptominer (XMRig), and see how quickly a normal server connected in the Internet can be used for mining… Read more
-
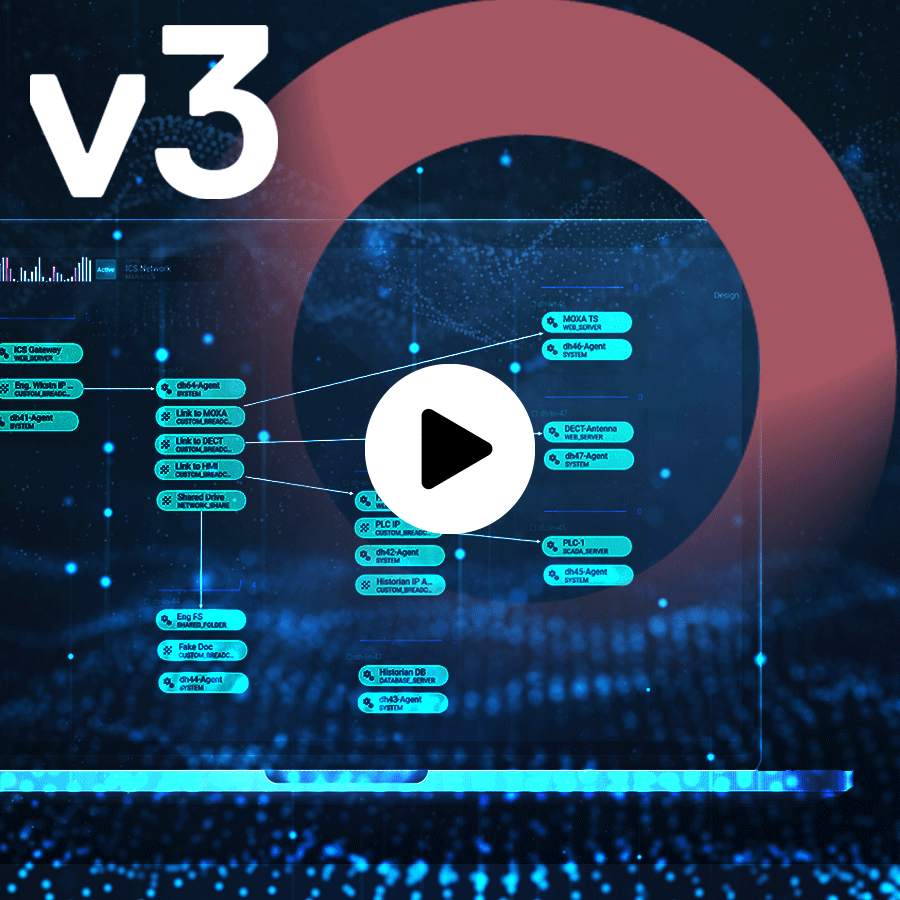
ActiveLures™ are designed to attract adversaries into the CounterCraft ActiveSense Environments. Read more
-
Looking at how to use real time kernel monitoring for shellcode detection. Alonso Candado discusses the challenges faced when trying to detect shellcode at runtime, usin the examples of hooking syscalls via hypervisor EPT feature and detecting shellcodes from kernel callback. Read more