Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
In part one, we talked about how the technology deployed to deal with the insider threat, such as cyber deception, must deter, detect, and disrupt. Here we address rules two and three: Threat Types and Threat Activities. Read more
-
Last week, CounterCraft attended the Gartner Security & Risk Management Summit. These are some of the key points we took away from Pete Shoard’s presentation, that answer some of the questions you might have about cyber deception. Read more

-
Cyber deception can be deployed to deal with insider threats effectively and rapidly. How does it relate to Gartner’s “rule of three”? Read more
-
MITRE has released Shield this August to great community approval. Shield is the defensive partner to the well known ATT&CK matrix that defines threat actor activity. Shield is a set of defensive techniques that defend and protect against specific threat actor actions. Read more

-
With cyber deception, you can take advantage of your knowledge about your assets and network, information that your adversaries don’t have, to build a more resilient security architecture. Read more

-
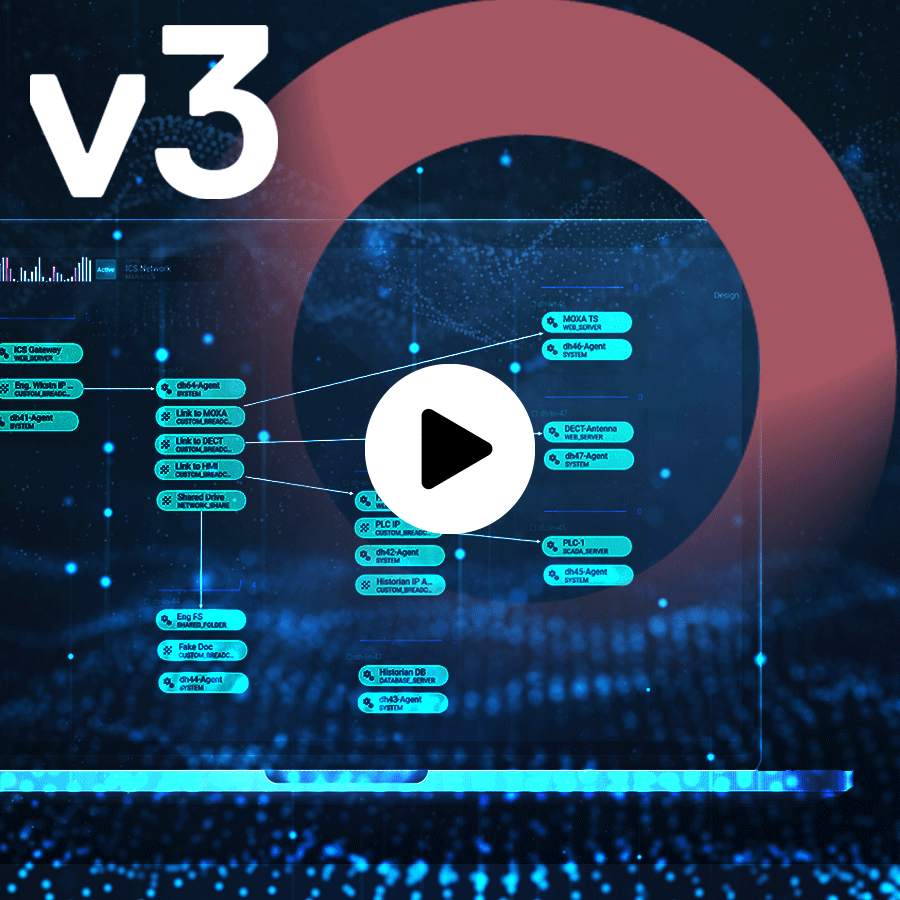
Deception technology can be used to add zero impact security and gather valuable first-hand threat intelligence on those who are targeting your OT systems, with no risk to business continuity. Read more