Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
Categories: Product Features
Deception tech allows enterprises to detect more threats and to detect a higher order of threats. Read more

-
See full-spectrum cyber deception and ground-breaking threat hunting in action at South Expo booth 3342 Read more

-
This is part two of a two-part series to describe how CounterCraft deception technology can be used to protect Microsoft Active Directory. Read more
-
Active Directory (AD) a very obvious target for attackers. The purpose of this blog post is to describe an example of how deception technology can be used to detect (and therefore control) an attacker as they attempt to breach your AD installation Read more
-
Blogs written by our deception and threat intelligence experts. Learn how to accelerate threat detection and add threat hunting capabilities to strengthen your security strategy. Read more

-
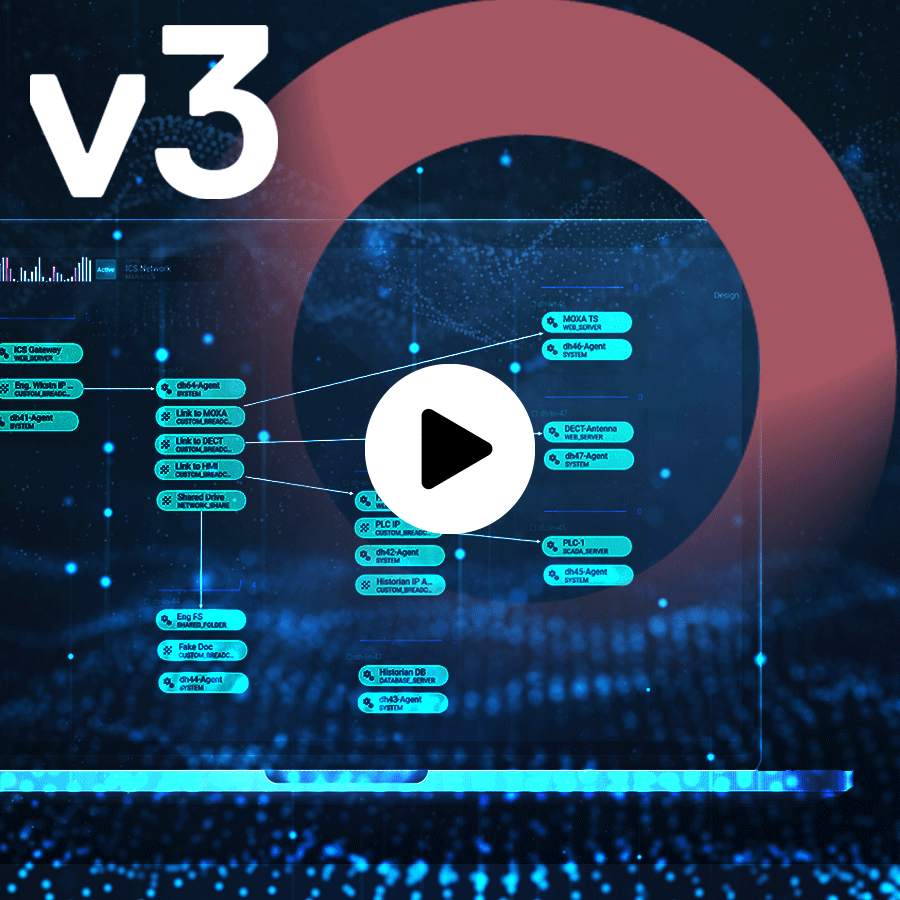
Cyber deception is now receiving a lot of interest. But how does it work? Our Product Manager, Richard Barrell, deconstructs deception in this enlightening overview of CounterCraft 2.0. Read more