Cyber deception is the most effective way to identify threat actors in any organization’s network. CounterCraft delivers actionable threat intelligence across industries.
-
Using Deception to Protect Active Directory Pt. 1
Active Directory (AD) a very obvious target for attackers. The purpose of this blog post is to describe an example of how deception technology can be used to detect (and therefore control) an attacker as they attempt to breach your AD installation Read more
-
Our top 5 most read cybersec blogs of 2018
Blogs written by our deception and threat intelligence experts. Learn how to accelerate threat detection and add threat hunting capabilities to strengthen your security strategy. Read more
-
Deception deconstructed: how CounterCraft 2.0 works
Cyber deception is now receiving a lot of interest. But how does it work? Our Product Manager, Richard Barrell, deconstructs deception in this enlightening overview of CounterCraft 2.0. Read more
-
How to Fight Threats in the Modern Age
Cyber attacks are attributed to one criminal group based on some IOCs, the type of tools used by the attackers, or their modus operandi. The truth is that attribution is often difficult to determine. Read more
-
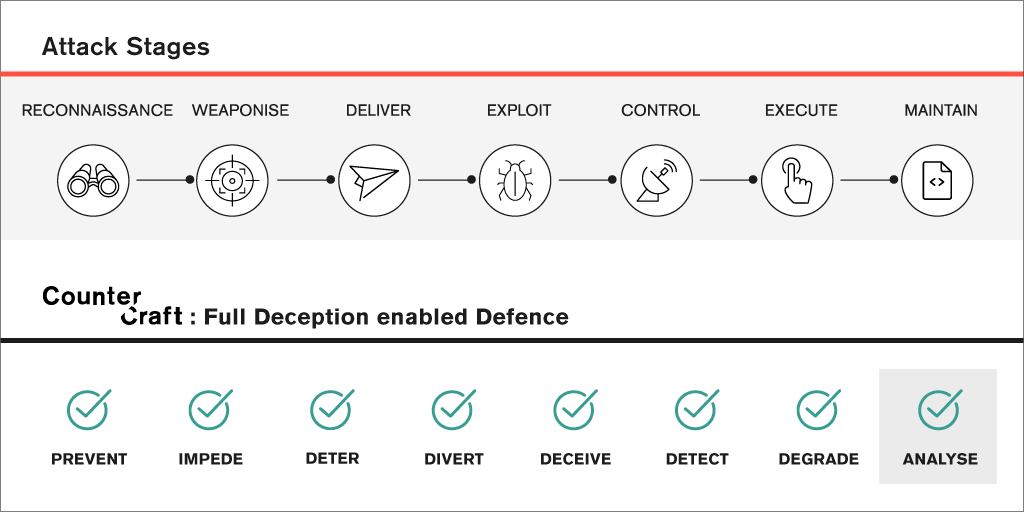
What can Deception do to Defend Across the Attack Lifecycle?
If your organisation is new to the concept of Cyber Deception as an emerging component in an enterprise defence in depth strategy, then we hope to introduce you to some of its value now. Read more
-
How Deception Technology Helps CISOs Meet the Challenges of Cyber security
CISOs and their security teams can use deception technology to significantly increase their ability to identify and deflect potential attackers. This is not just about security; organisations spanning every sector are currently embarking on ambitious digital transformation programs. Read more