Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
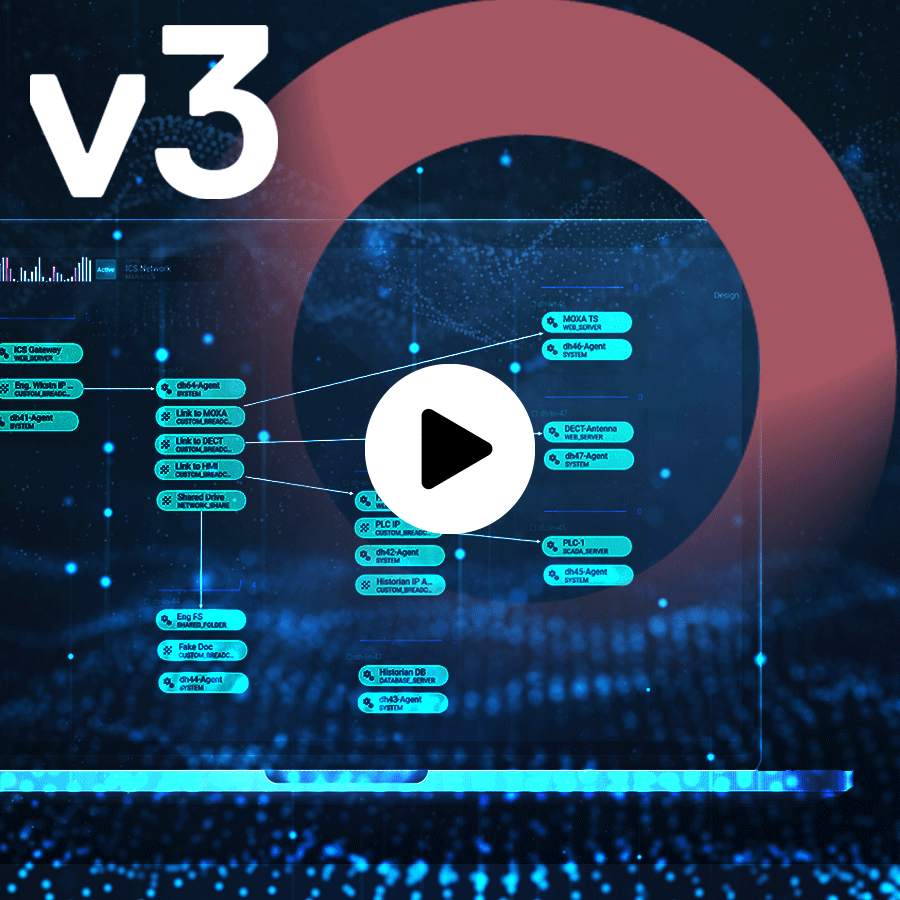
CounterCraft 2.6 excels in the five stages of deception identified by Gartner, basic threat detection, detection and response, production of local IoC and MRTI, integrated proactive threat hunting and active attacker engagement. Read more
-
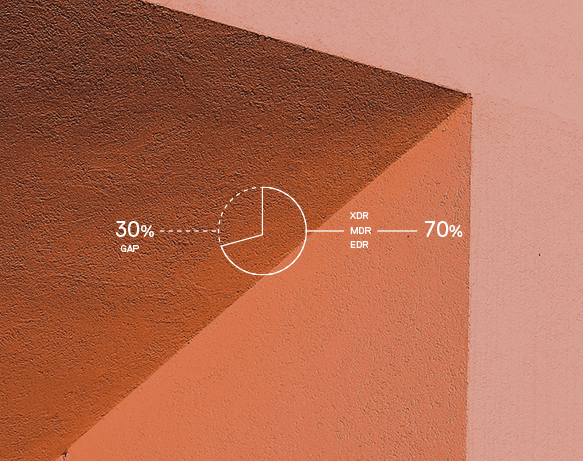
The market is full of security providers that offer Threat Intelligence solutions that seem interesting, but their usefulness in many environments is not so clear. Read more
-
CounterCraft 2.6 is here, and as we throw ourselves into our fourth visit to San Francisco’s Moscone Centre in a few weeks for RSA, we can’t think of a better way to embark on this new decade. Read more

-
Nowadays, few computers use Windows XP. However, many of the existing tools used by current threat actors for internal lateral movements do work in this operating system. Now you can use Windows XP devices in our deception campaigns. Read more
-
Categories: Company News
CounterCraft and PwC, leading cybersecurity companies, recently reached a global strategic collaboration agreement. PwC will provide digital counterintelligence consulting services and the CounterCraft Cyber Deception Platform to large international companies Read more

-
Categories: Company News
This is the perfect time to reflect on the year past and think about what the future will bring. So, before starting 2020 with renewed purposes about making your organization more secure, why not take a moment to re-read our top 5 blog posts of 2019? Read more