Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
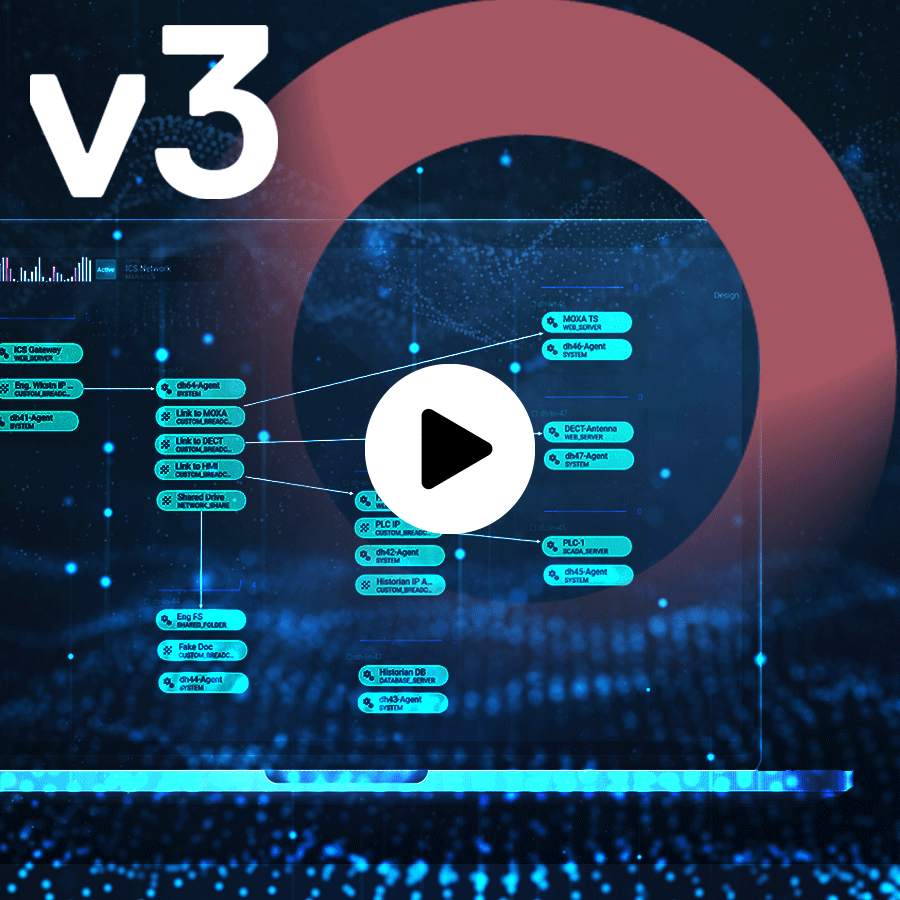
ICS security is challenging. See how Red Electrica used deception technology to prevent attacks on their OT systems. Read more

-
Working towards achieving zero trust in an organization is a move in the right direction to protect against cyberattacks. However, to truly defend against cybersecurity threats, an organization has to take an active defense approach to cybersecurity threats. Read more

-
Working towards achieving zero trust in an organization is a move in the right direction to protect against cyberattacks. However, to truly defend against cybersecurity threats, an organization has to take an active defense approach to cybersecurity threats. Read more

-
Categories: Cybersecurity Trends
Cybersecurity News June Edition. Click through to find out what our team of experts was reading and talking about this month. Read more

-
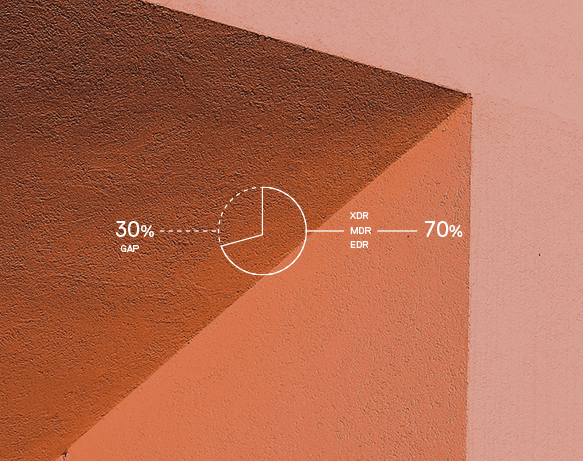
The United States National Security Agency (NSA) issued a Cybersecurity Advisory on a recently discovered use of Living Off the Land Binaries (LOLBins) techniques by Volt Typhoon to evade detection by EDR, XDR and SIEM solutions. CounterCraft’s deception technology alerts on LOLBins automatically—and we ran a test this week to prove it. Read more
-
EDR—the cybersecurity solution that is a vast improvement over mere endpoint protection and anti-virus solutions….right? Well, there is one small hitch—EDR is a reactive approach. EDR tools function on a reliance of behavioral analysis, meaning the attacks have already happened and now your team has to race against time to remediate them. EDR avoidance is… Read more