Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
Threat intelligence used to be the domain of a few cybersecurity analysts who spent their time tracking global bad actors and piecing together knowledge of their tactics, techniques, and procedures (TTPs). Today, any organization can subscribe to threat intelligence services and feeds, using the data to predict and identify threats targeting their business. The numerous… Read more

-
According to Verizon’s latest data breach report1, 70% of attacks are perpetrated by external threat actors. Lack of visibility into external attack surface assets and vulnerabilities is one of the main obstacles global banks face when trying to protect their perimeter effectively. Our cyber deception platform offers one of the best technologies for dealing with… Read more
-
Categories: Cybersecurity Trends
Cybersecurity news in February. Click through to find out what our team of experts was reading and talking about this month. Read more

-
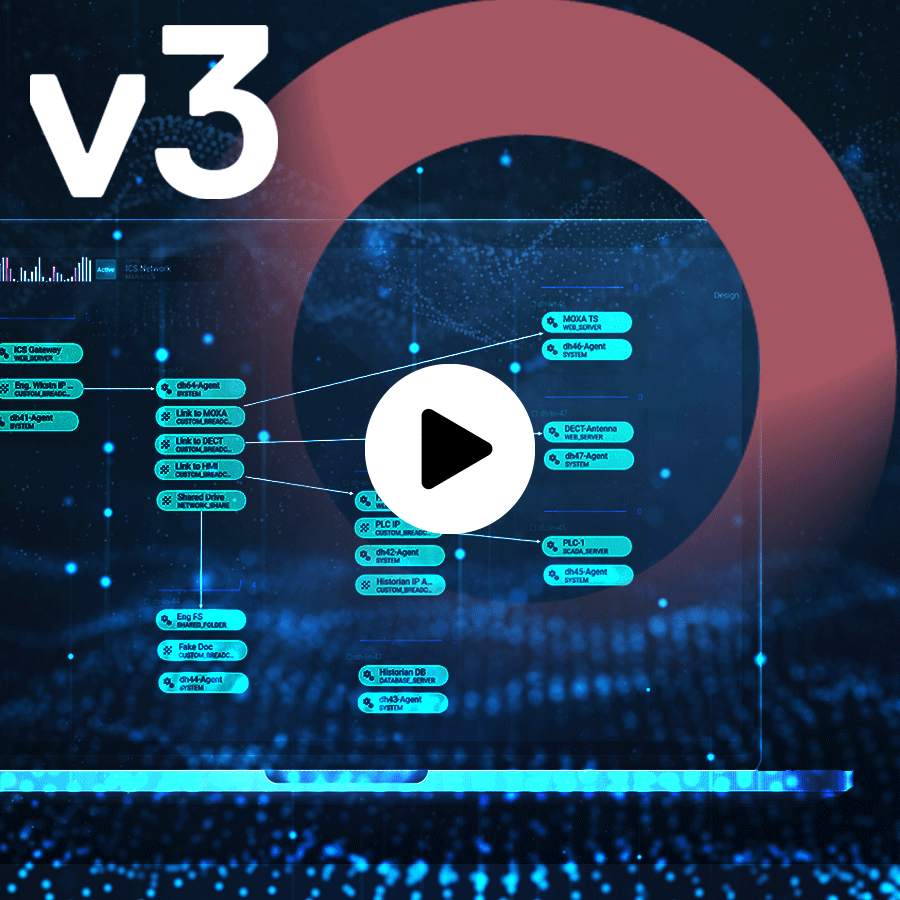
Complexity. Threat analysts work with lots of data and need powerful tools to navigate and restructure it into specific narratives. They also need dashboards that convey status at a glimpse for a more agile and actionable workflow, no matter how complex the system is. But more complexity and data doesn’t mean bigger tables and shinier… Read more
-
Categories: Company News
Creating and launching a new website is one of the most important (and stressful!) projects a marketing team can undertake. More often than not, a new site accompanies a revamp of a brand’s identity, a critical labor of love that most marketers only get a chance to do a few times ever in a career.… Read more

-
Categories: Deception Technology
Cybersecurity news in February. Click through to find out what our team of experts was reading and talking about this month. Read more